I must be going through a honeypot and honeytoken phase. This probably happens for a lot of folks in cyber security when they come across decoy honeypot concepts. Honeypots are systems and application services that can mimic request and response, be interactive, or a full system with the express purpose of detecting attackers as they engage with the decoy system to alert defenders and track the attackers techniques.
I tend to think of honeypots and honeytokens operations as a old Nintendo game called Spy vs. Spy based on Mad Magazine’s cartoon characters. Even the characters don white and black hats.
In the game you must find secret briefcase and other spy items to escape, those items are in furniture, wall art, or closets scattered through out the rooms of a building and it’s floors. Along the way you can place traps like bombs, acid rain, or electricity in those same objects so that the black hat spy can be slowed down and also alert you on a map to where he might be. It’s all about imposing costs on the black hat spy, slowing him down, alerting you to his presence and giving you an advantage to collect the items and exit the building before the black hat spy does. A lot of those concepts in the video game have parallels and can provide inspiration to cyber security operations looking to defend and placing honeypots and honeytokens.
Awhile back while reading a excellent primer by Chris Sanders called “Intrusion Detection Honeypots“ I came across in my research a really impressive open source project collecting the different software honeypots out there and using docker images of these in a clever architectural pattern that creates a wonderful platform. T-Pot
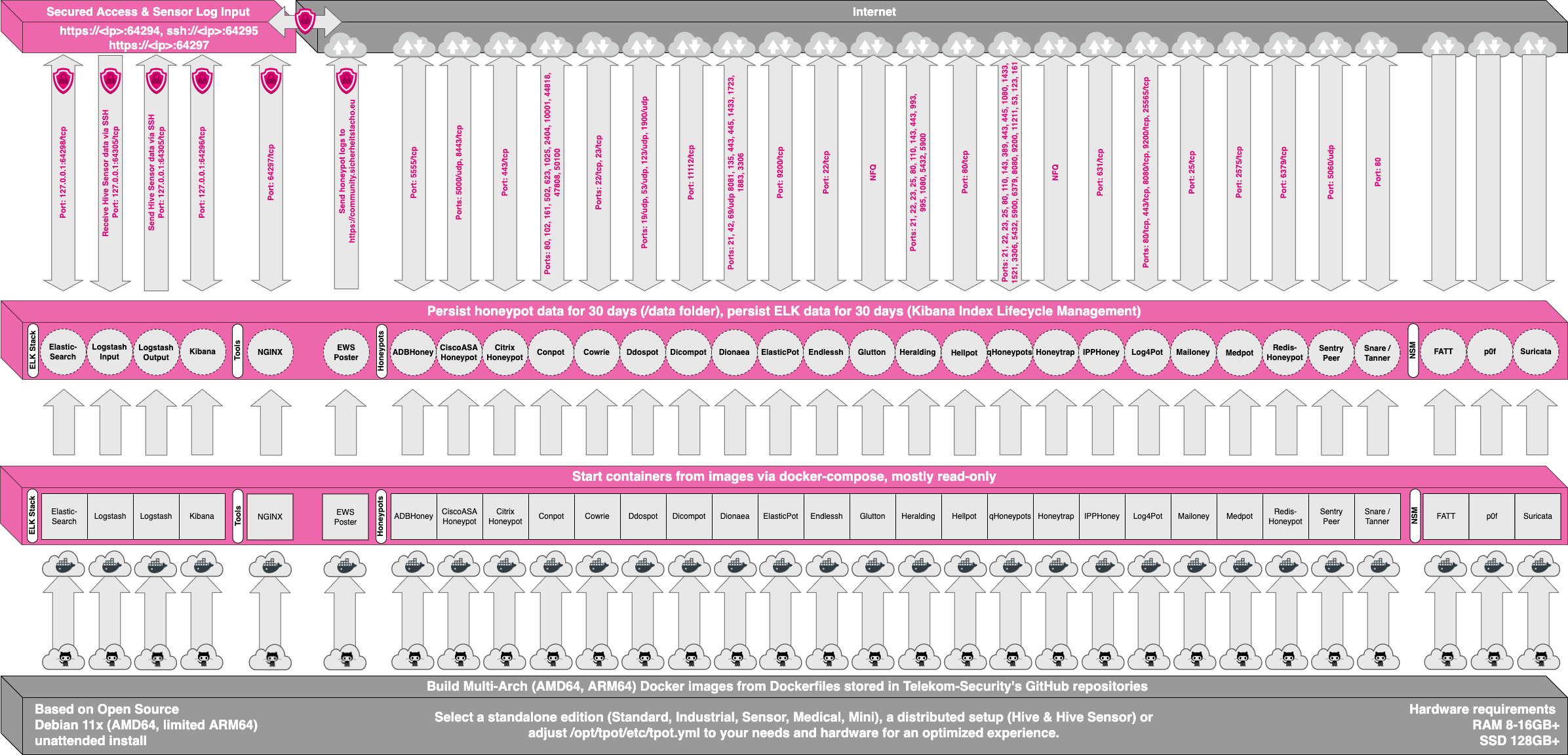
Below is an image of this amazing platforms software architecture to get a sense of the scale and depth deploying T-Pot can provide.
In the middle pink stack you will find left to right:
ELK stack allows you to search, visualize attacks via dashboards, and collect and send logs
Nginx to help guide some traffic
EWS Poster to opt in and send the telemetry to HPFeeds, Opt out if needed however sending data to Sicherheitstacho
22+ Honeypots, focusing on protocols, vulnerabilities, and with different degrees of interaction and collection.
Network Enrichment and Monitoring: Fatt (Network metadata), Suricata (IDS,IPS,NetSecMon), p0f (Passive fingerprinting)
One of things I wanted to do was get the unattended install of T-Pot and wrap in a easy to deploy Azure template so defenders can leverage this goodness in their Azure virtual networks or on the periphery facing the Internet.
After a little trial and error a working example with instructions has been completed click here to deploy onto your Azure virtual network:
At a high level T-Pot will provide you the following as a defender:
A Azure VM ready to go in your virtual network of choice with certain NSG Rules
T-Pot and many different types of Honeypots you can expose via a NSG Rules to your private networks or Internet.
Really great set of security tools on https://yourazpip:64297 like:
CyberChef - The Cyber Swiss Army Knife
Elasticsearch - ESQL Query your way through honeypot event logs
Kibana dashboards - A bunch of dashboards centered around the Honeypots
Attack Map - A high level world map and statistics of all the Pew Pews occuing especially if you leave open a port or a few on the Internet
SpiderFoot - a open source intelligence (OSINT) automation tool
& more
With some time coming up this summer I am hoping to extend this further with a blog on “How to integrate with Microsoft Sentinel guide” and eventually update the Azure deployment to fully integrate the Logstash service automatically with Microsoft Sentinel’s plugin without manual steps.
Other stretch assignments may find me building Sentinel playbooks to use with incidents and entities calling back to the T-Pot’s hosted tools like SpiderFoot, CyberChef, Elastcsearch’s APIs. SpiderFoot’s exposed Scan API could be used for enrichment purposes of entity information. CyberChef’s recipes API could be invoked via Sentinel potentially for certain use cases ? Also Conpot (ICS SCADA Honeypot) is of interest to see if we can place alongside Defender for IOT in a OT environment.
In the meantime keep laying those traps and increase those imposing costs on attackers and would be black hat spies.





Excellent