Defender for Servers - Failed MDE. VM Extension Report
The Fundamental Elements of PowerShell Reporting Script Framework
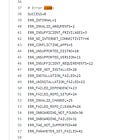
Sometimes during enterprise deployments using Defender for Servers auto deployment, errors can occur with the onboarding of Azure virtual machines or Arc connected servers into Defender for Endpoint.
To access the PowerShell Script for reporting errors see here:
As an example we will use a Azure Linux Server, Defender for Servers auto deployment works as follows:
VM Extension MDE.Linux is deployed to Azure Linux Server
As part of deployment the VM extension MDE.Linux downloads mde_installer.sh and inside the server and executes script, awaiting for a response back from script, either error code or status code 0 successfully.
The MDE.Windows and MDE.Linux extensions push a onboarding script but does record the results back in the VM extension. This allows for a way to collect error statuses easier from the Azure cloud management plane.
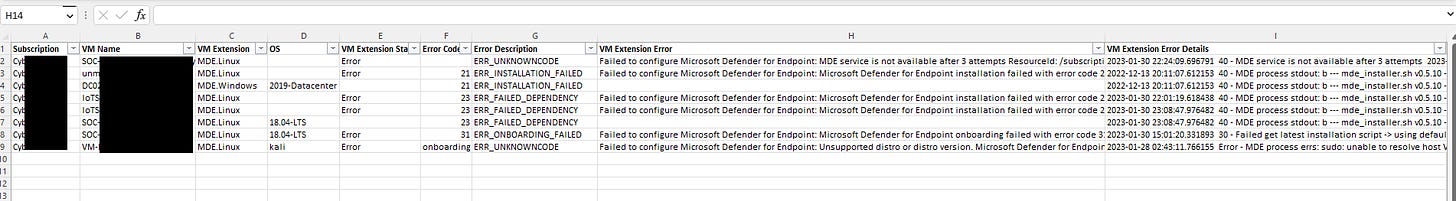
While the following Defender for Cloud Onboarding Workbook is a great starting point for looking at deployment status in a enterprise context. The workbook relies on Azure Resource Graph which does not store detailed error messages and sub messages returned back from onboarding script in the VM Extension attached to the Azure VM. This is where scripting using PowerShell or Azure CLI can come in handy when wanting to get all kinds of details from Azure Resource Management.
With the help of a colleague Chris Jackson we wrote a Quick PowerShell Script that can collect additional information to help you Filter and Group by errors to understand MDE. VM Extension failures at enterprise scale. The report can help you determine if patterns exist, so by solving on one server you know which servers to target the fix to solve for the rest.