Azure Activity logs (think audit logs) are wonderful, they capture almost all the API activities occuring in Azure Subscriptions. Created resources, modified resources, Delete resources, even when people read keys from storage, key vault, ect. One thing they will not capture is a Read API call on a resource unless it was something like a key. This is to reduce the amount of events \ logs one may want to store. Imagine writing events each time someone vistied the Azure Portal, it would be too many.
One of the Activity Log events some folks in IT, Networking, and Security may want to know is when a NSG Rule is Created or Updated. Within the Activity Log event itself you will find some very good information but not the actual ACL rule details like the 5 tuple settings themselves. Did someone Allow All traffic to 3389 ?
"authorization": { "action": "Microsoft.Network/networkSecurityGroups/securityRules/write", "scope": "/subscriptions/XXXXXXXX-xxxx-xxxx-xxxx-XXXXXXXXXXXX/resourcegroups/rgPaaS-Security/providers/Microsoft.Network/networkSecurityGroups/AFD-NSG/securityRules/VNET-Allow-All" }, "caller": "someone@contoso.com", "ipaddr": "1.1.1.1", "name": "Someone Somewhere", "category": { "value": "Administrative", "localizedValue": "Administrative" }, "eventTimestamp": "2020-05-19T18:30:43.3351037Z", "id": "/subscriptions/XXXXXXXX-xxxx-xxxx-xxxx-XXXXXXXXXXXX/resourcegroups/rgPaaS-Security/providers/Microsoft.Network/networkSecurityGroups/AFD-NSG/securityRules/VNET-Allow-All/events/e8617160-fe72-4260-9480-4008f26214dc/ticks/637255098433351037", "level": "Informational", "operationId": "ef601558-ab70-43a5-86c0-dd5985ad1e0d", "operationName": { "value": "Microsoft.Network/networkSecurityGroups/securityRules/write", "localizedValue": "Create or Update Security Rule" }, "resourceGroupName": "rgPaaS-Security", "resourceProviderName": { "value": "Microsoft.Network", "localizedValue": "Microsoft.Network" }, "resourceType": { "value": "Microsoft.Network/networkSecurityGroups/securityRules", "localizedValue": "Microsoft.Network/networkSecurityGroups/securityRules" }, "resourceId": "/subscriptions/XXXXXXXX-xxxx-xxxx-xxxx-XXXXXXXXXXXX/resourcegroups/rgPaaS-Security/providers/Microsoft.Network/networkSecurityGroups/AFD-NSG/securityRules/VNET-Allow-All", "status": { "value": "Succeeded", "localizedValue": "Succeeded" }, While Azure Security Center's recommendations can alert you to this, and you could setup workflow automation as well, one other approach I recently undertook was using Azure Monitor's Alerts and Action Groups.
First you need to create a Logic App, I have built one here:Audit-NSG
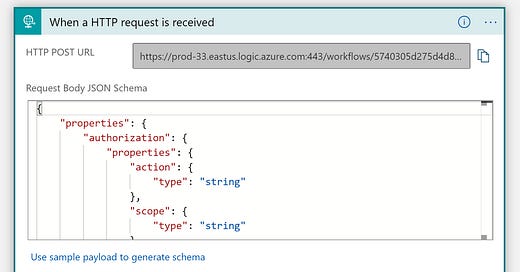
At a high level the Logic app will use Requests as the trigger. This allows for an event driven approach and Azure Monitor Alerts and Action Groups will use this as the trigger.
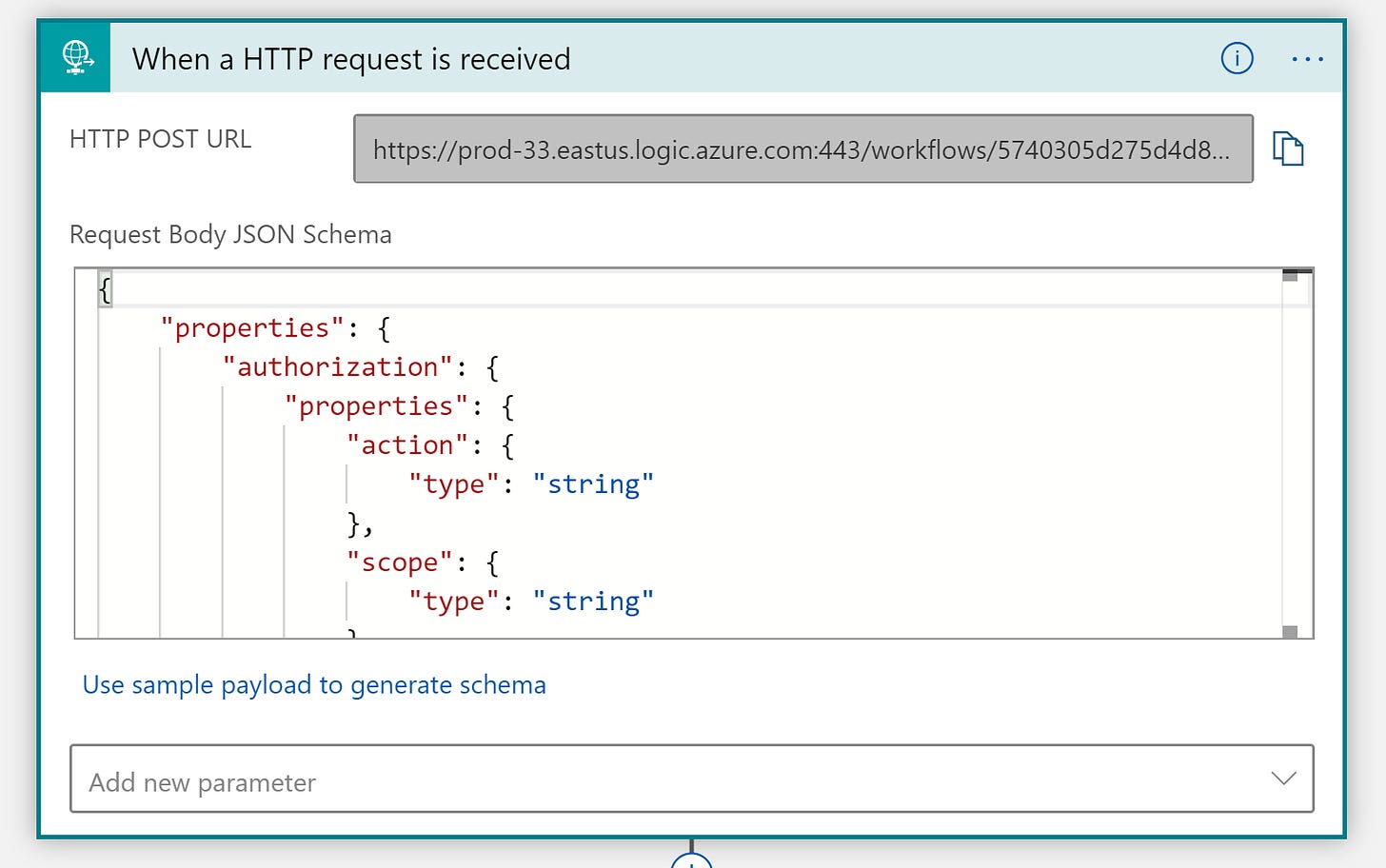
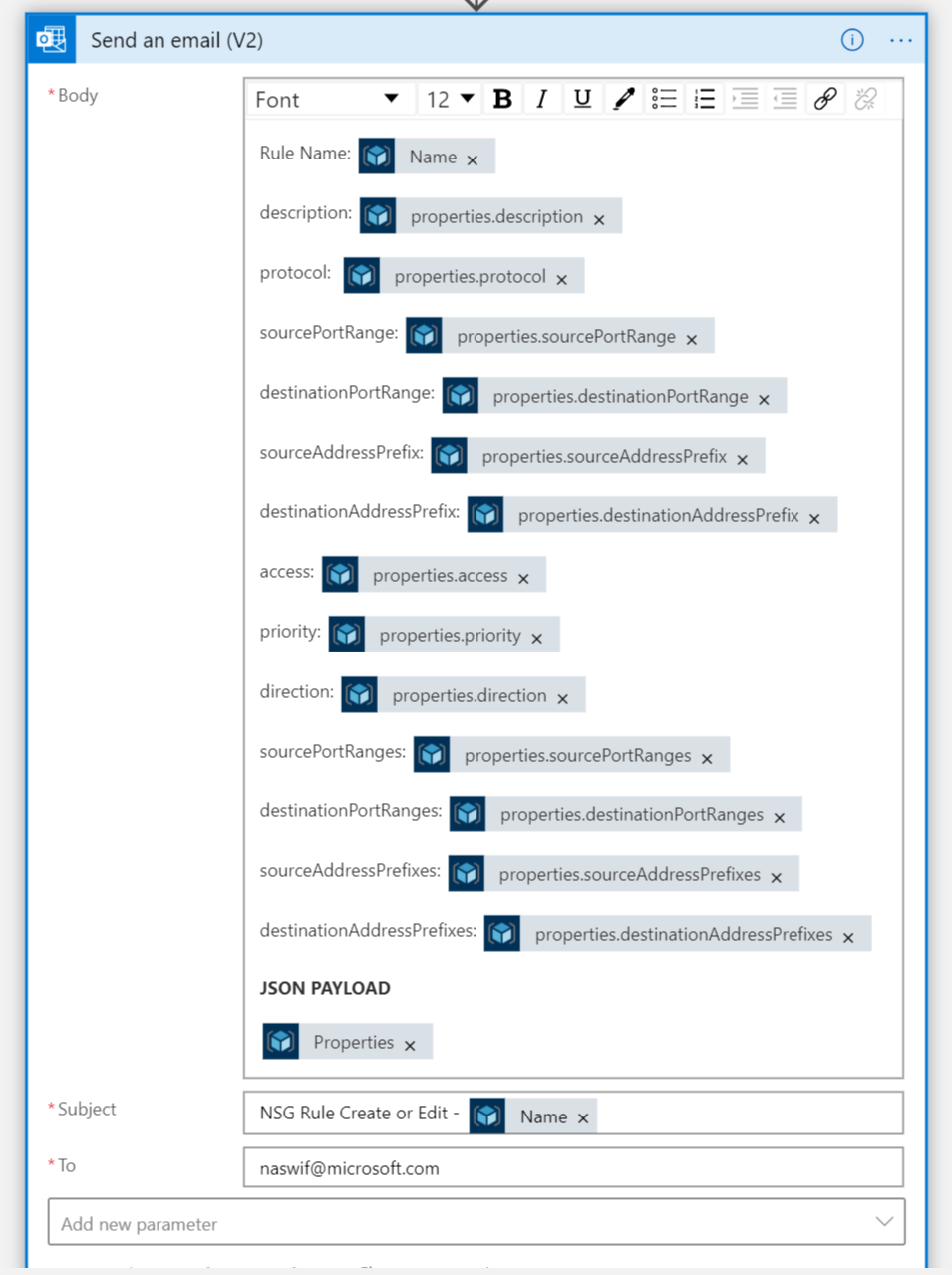
Instead of HTTP Requests action you will use the Azure Resource Manager Connector | There is a lot you can do with this and covers your needs.
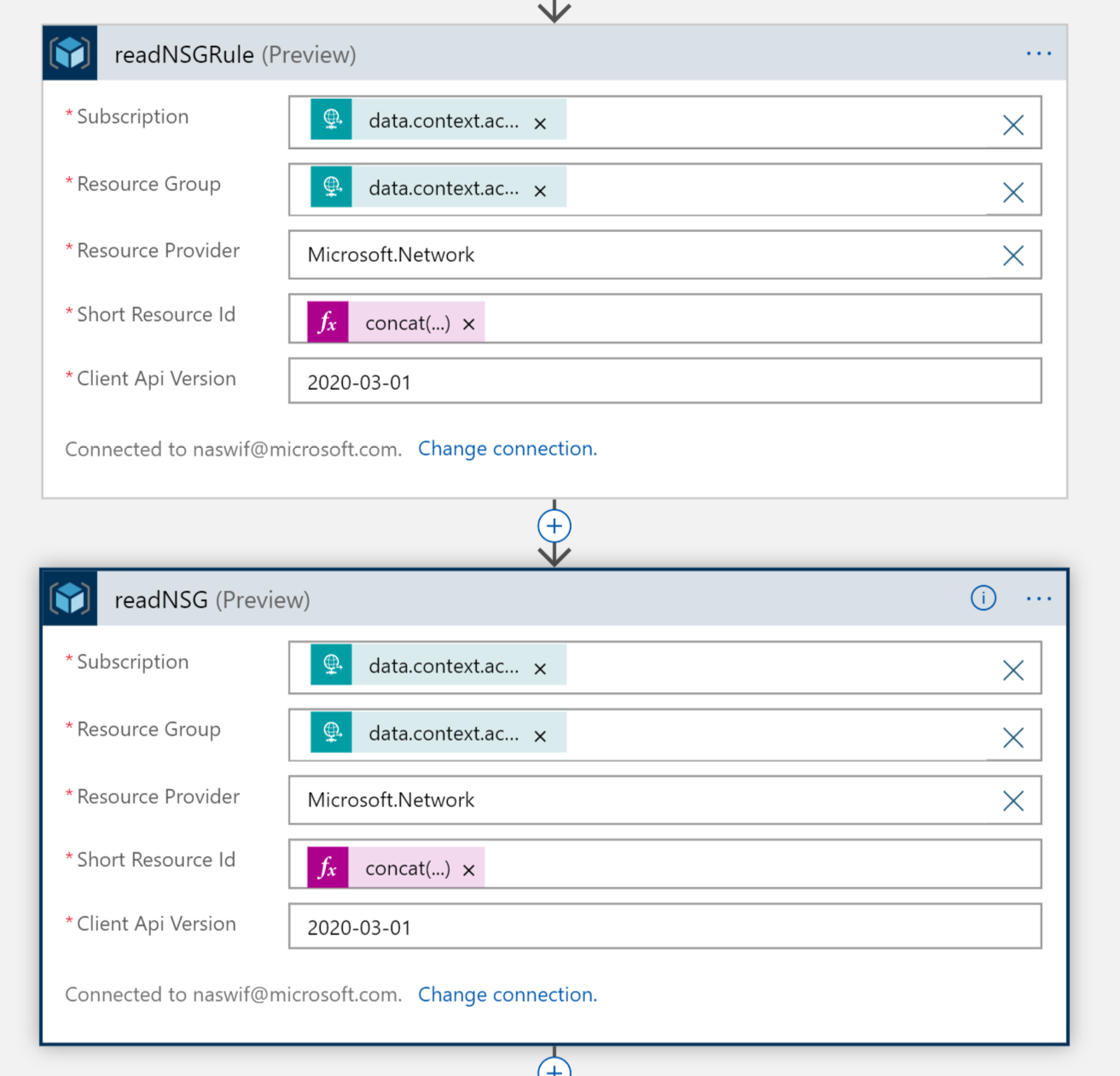
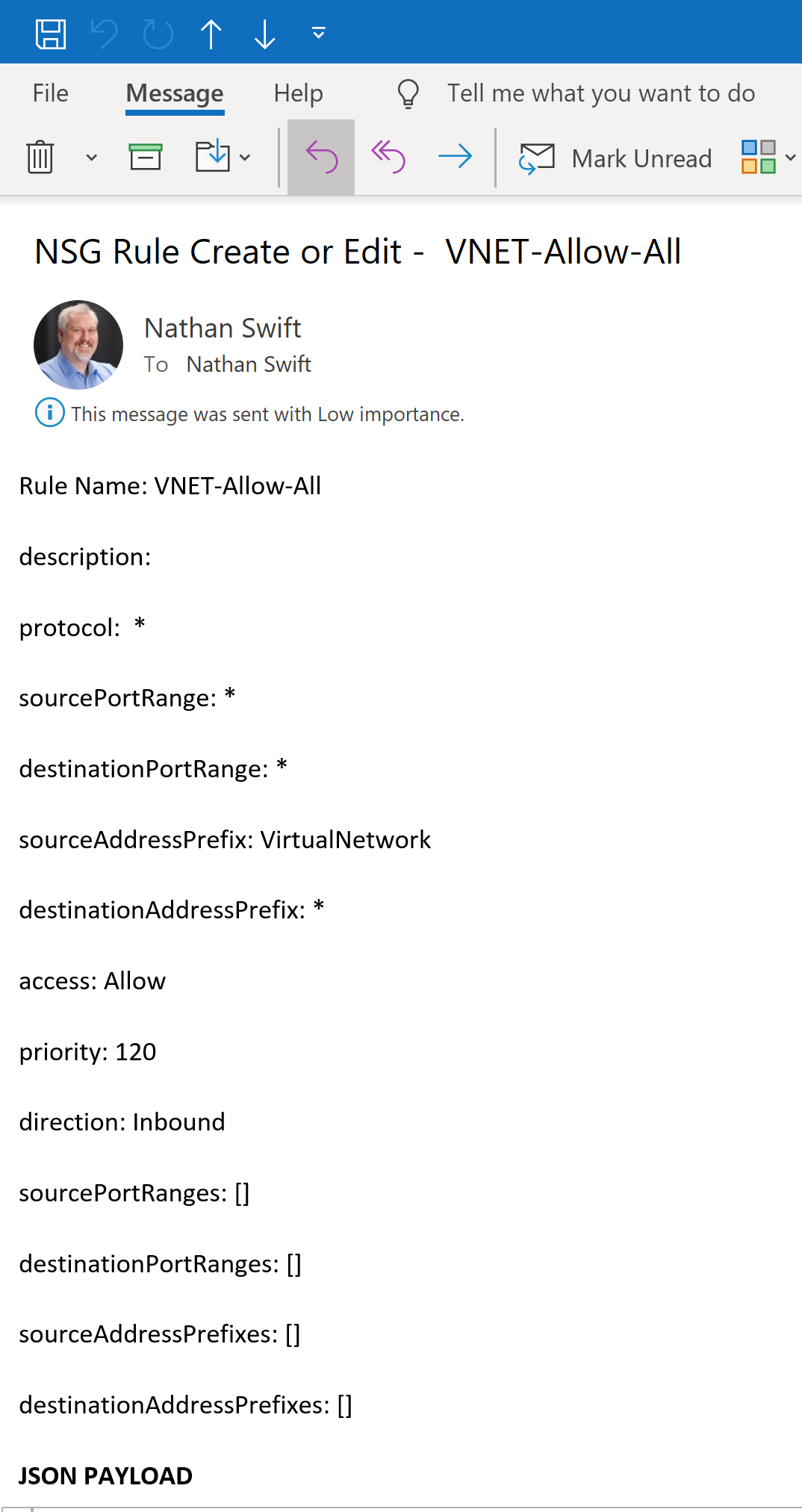
You have now collected all the details of the NSG Rule, we could do a lot with this, write a conditional check for too permissive rules and then delete the rule. In this example we will send an email regarding the NSG rule details.
Next we will need to setup a Azure Monitor Alert to trigger on
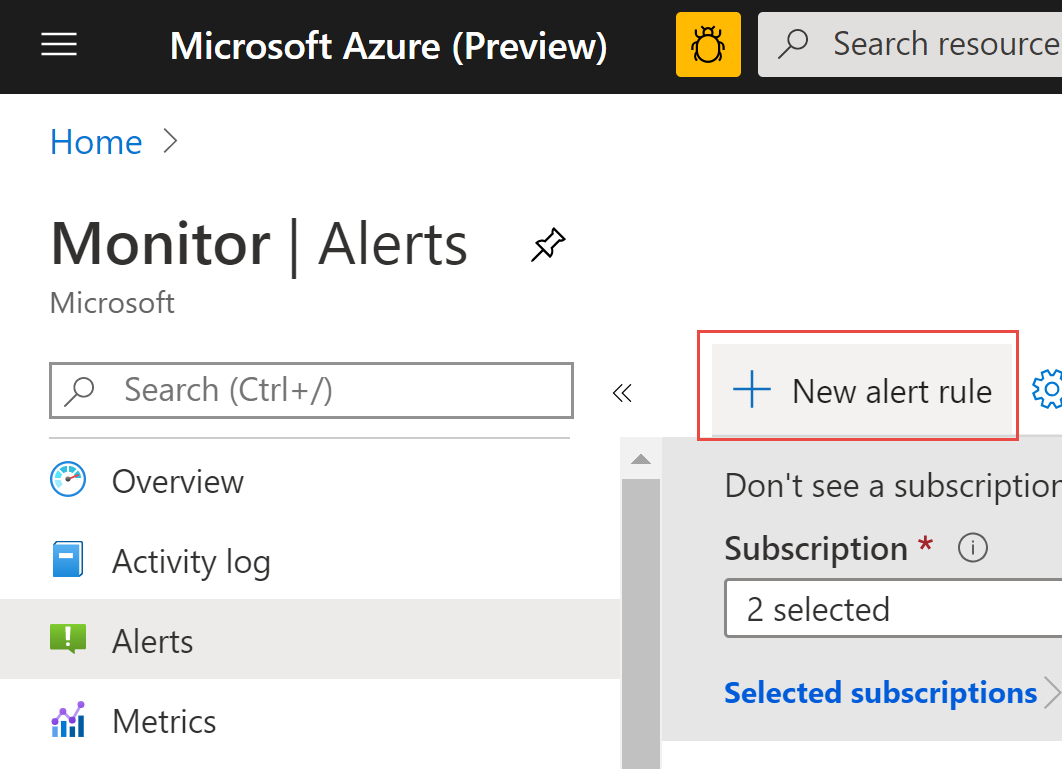
Within Azure Monitor create a new alert rule
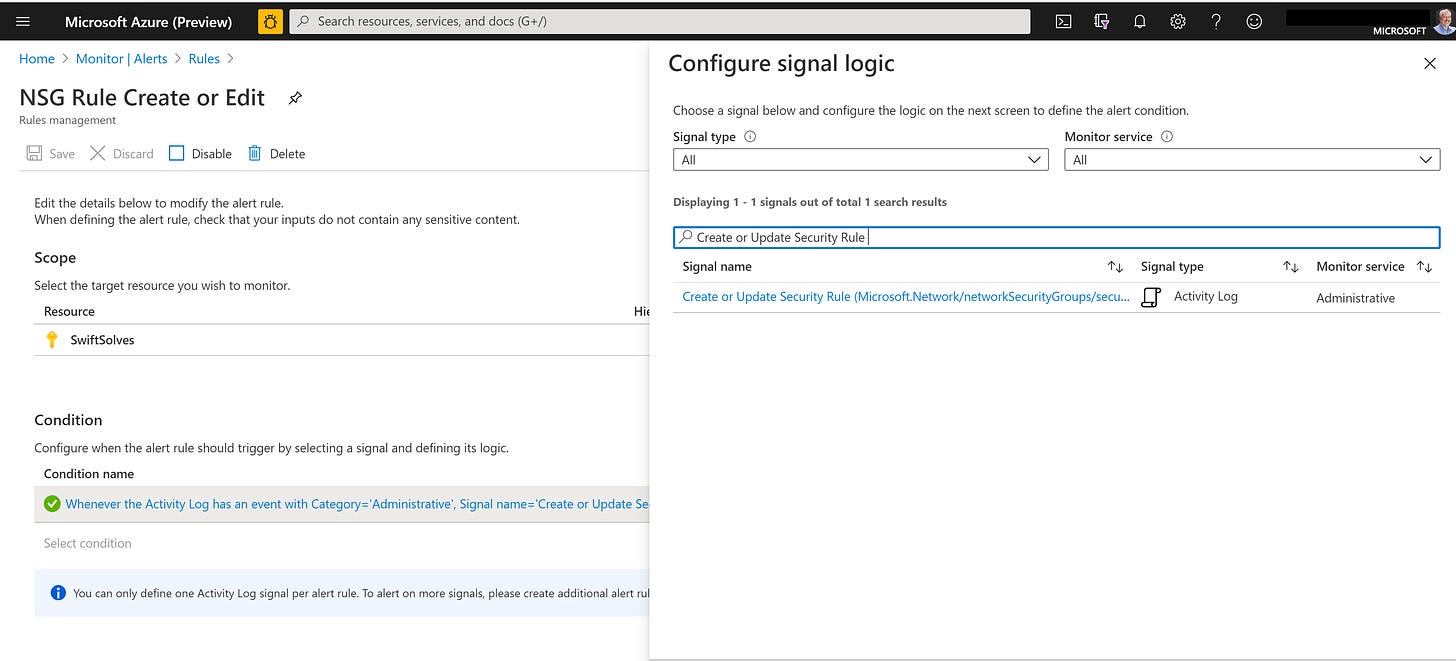
For the condition to alert search for Create or Update Security Rule
Set the additional conditions for Informational, Succeeded, All services and users
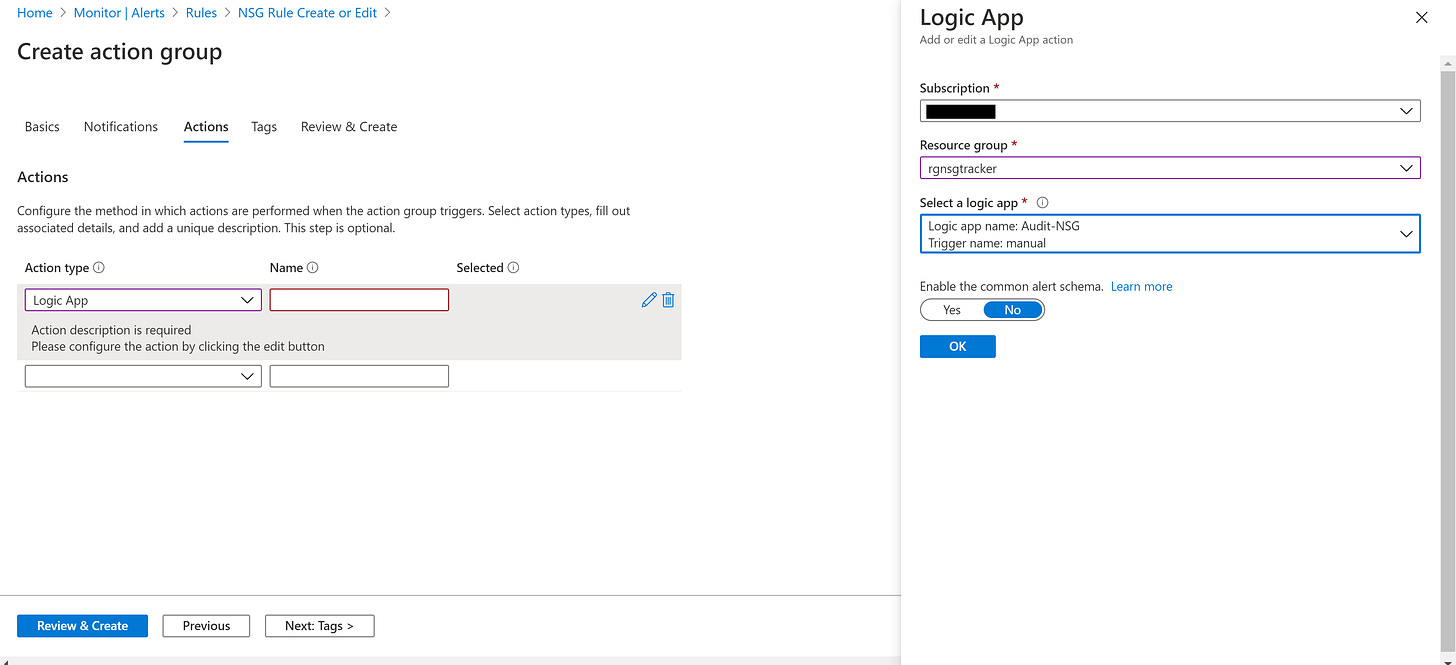
Finally create a action group to use a Logic App and define the Audit-NSG o be ran.
Now when a NSG rule is created or modified your team will recieve an email with the NSG Rule details.