Recently I have been examining some ways to bring in Oracle Cloud Audit Events into Azure Sentinel. As I go along testing and building this I plan to send a few shorts around my findings and hopefully clarify around this subject.
The basis of this using the Audit Events from a REST API
We will need to pass an Oauth token in the request, but to do that we need to generate a a token and also register what Oracle describes as a Confidential Application (service principal like a app id and key secret) to be used to generate a token.
In todays outline we will cover just that how to generate the Confidential Application to be used.
To follow along you can sign up for a Oracle Cloud Trial here: https://www.oracle.com/cloud/free/
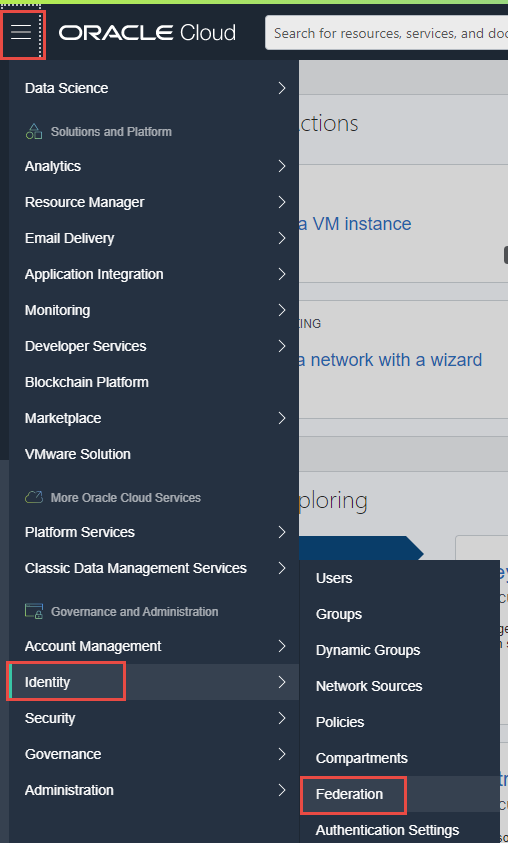
Once you have signed up and confirmed Oracle's documentation mentions going to ICDS URL to generate the Confidential Application, this URL or portal is actually different from the Oracle Cloud Console, to find your ICDS URL, using the Oracle Cloud Console - https://www.oracle.com/cloud/sign-in.html navigate using the top left corner hamburger bar: Identity -> Federation
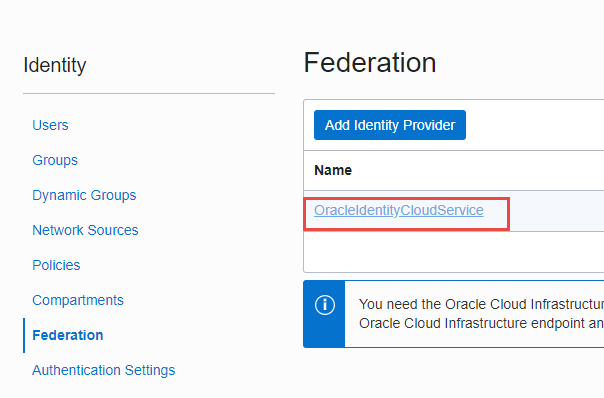
Click on the Oracle Identity Cloud Service
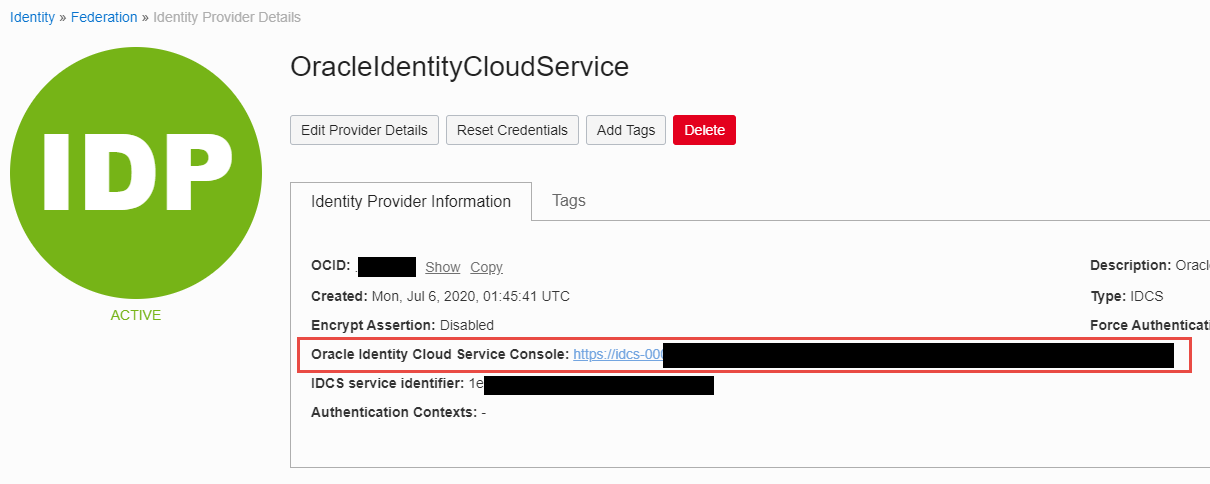
YOu now have the Oracle Identity Cloud Service Console URL: NOTE the FQDN of this url will be used later in PowerShell to make API calls
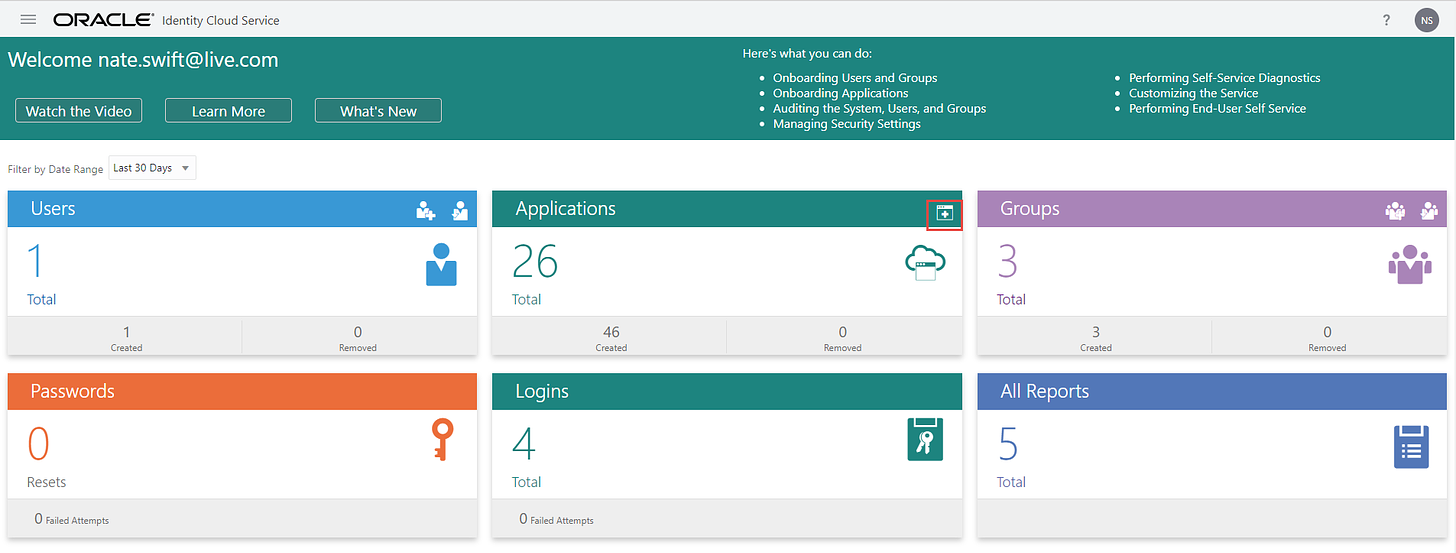
With the URL log into the Identity Console and click the Add Button for Applications
Choose a Confidential Application
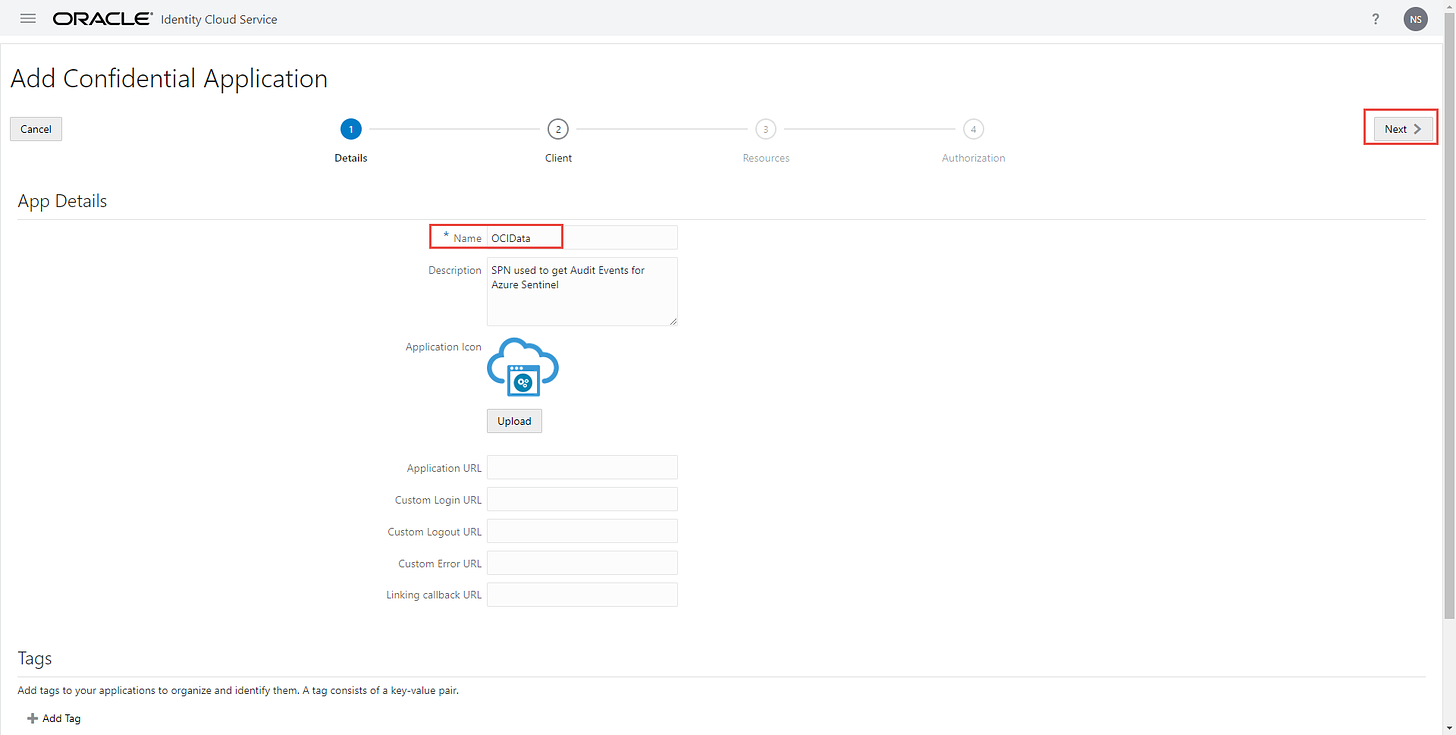
Supply a name and click next left hand side
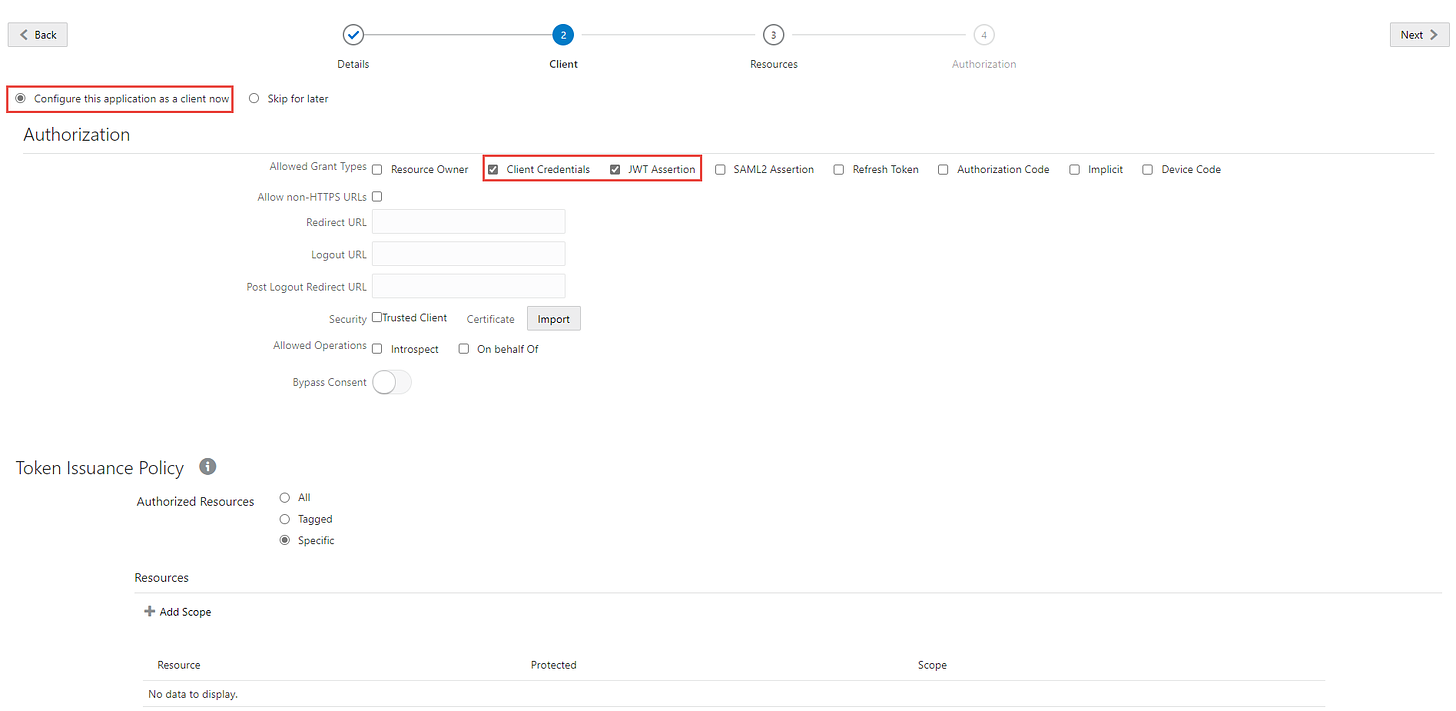
Click the configure the application as a client now radio button to expose additional settings
Check the Client Credentials and JWT Assertion boxes
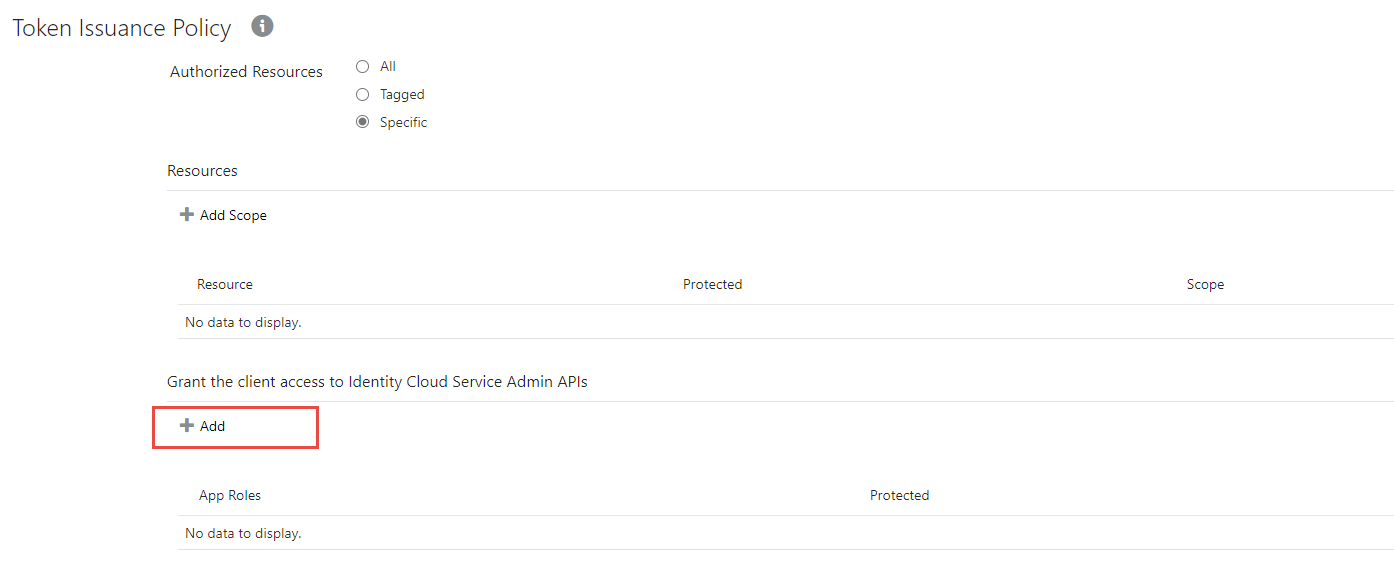
Scroll further down and add a App Role
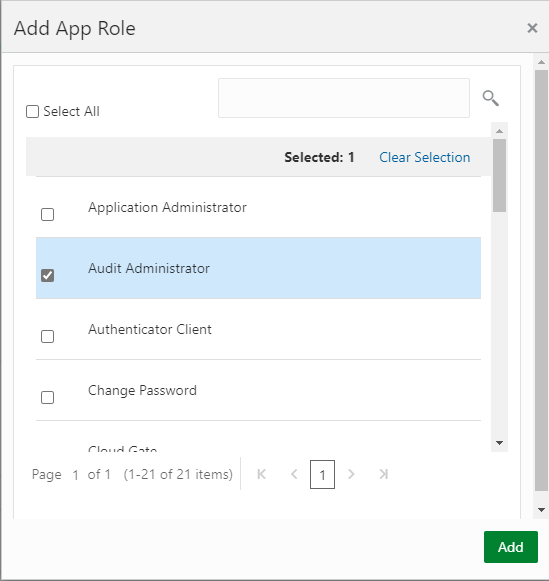
As of this time I am still testing things out to find least privileged role, so while testing I may have given too many permissions. I am testing with Audit Administrator and Identity Domain Administrator
Find role and Add and click Next
Click Next again
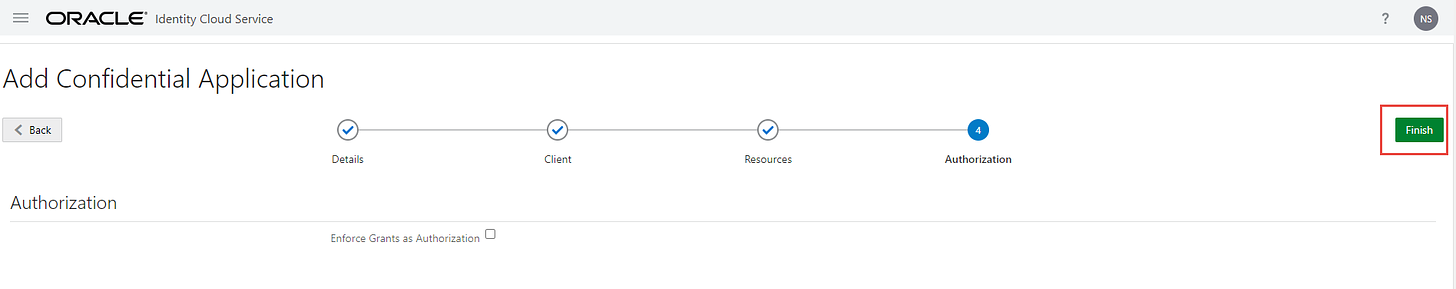
And click Finish
You will be prompted with a Client ID and Client Secret please record these, note that you can go back and reveal them again in the portal.
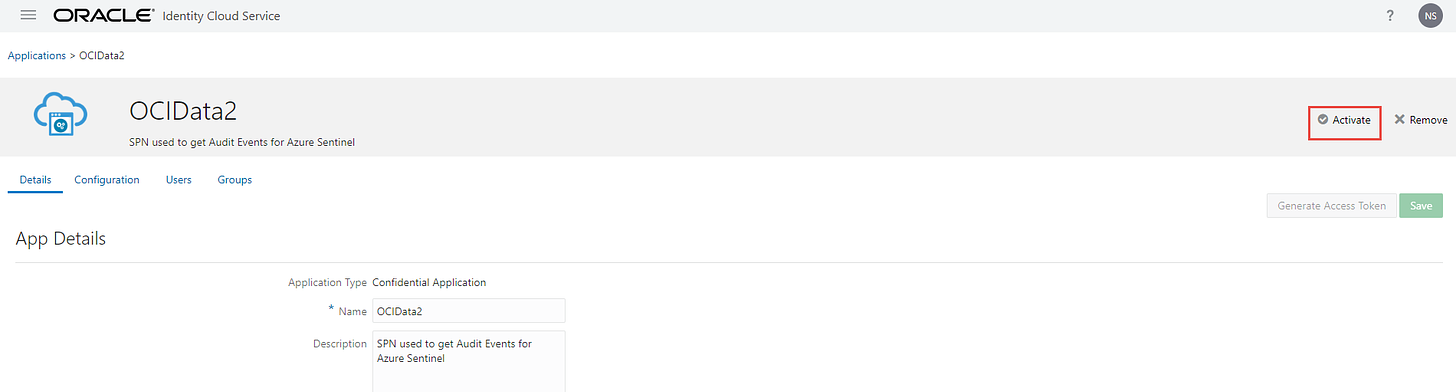
You will be brought to the newly created application in the top right and this is important click the activate button:
Now that the application is activated we have one final step. The API to generate a token has a header Authorization, that value is a base 64 encoded string of our copied values
To create the string just place the ClientID:ClientSecret
Like ###xxx##xxx###xxxx########c8be8e:xx##xx##-###x-#xx#-#x##-xxx###x####x
With the formed string you can base 64 by using a web b64 encoder or if you want to run it privately see the link below under Step 2:
https://docs.oracle.com/en/cloud/paas/identity-cloud/rest-api/OATOAuthClientWebApp.html
we can use IDCS URI and Base 64 encoded ClientID:ClientSecret to generate a oauth bearer token in PowerShell in Pt 2.
You can continue to follow in Part 2
As a reminder the complete script can be found here: https://github.com/swiftsolves-msft/PowerShell-Scripts/blob/master/Get-OIDCSAuditEvents.ps1
Sources:
https://docs.oracle.com/en/cloud/paas/identity-cloud/17.3.6/rest-api/OATOAuthClientWebApp.html