Good morning while working through the excellent documentation of Azure Security Benchmarks for Logic Apps I came across 1.4 Deny communications with known-malicious IP addresses
Within the security guidance if your Logic App uses a request-based trigger type you should secure communications. One such way is to deny communication to the trigger by restricting the inbound ip address
So naturally when you work with Azure Security Center workflow automations where the Recommendation or Alert trigger in a Logic App, can be further secured by only being executed from within the Azure Ecosystem specifically the Azure Security Center service.
To do so head over to download Azure IP Ranges and Service Tags – Public Cloud
Within the file search for AzureSecurityCenter and you will find the IP Address Ranges to add.
To make the change in the Logic App
go to the Workflow settings blade.
change from any ip to Specific ip ranges
add each ip address range and click out of the field to create a new field to add the ip address range
Optional: you can also protect and prevent reading the inputs and outputs of the run history (see below)
Click Save
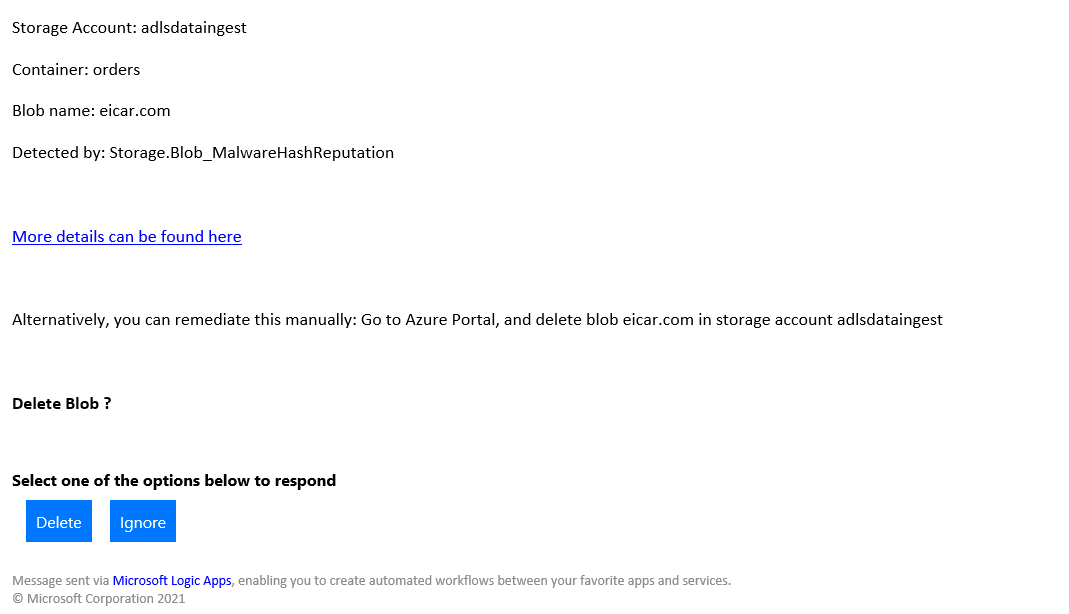
While testing I ran into another challenge, where I had a Logic App action send an email awaiting a user response from clicking an option in an email.
The URL link appeared to be calling the east us api management service, however after adding those ip address ranges from the document it was still failing.
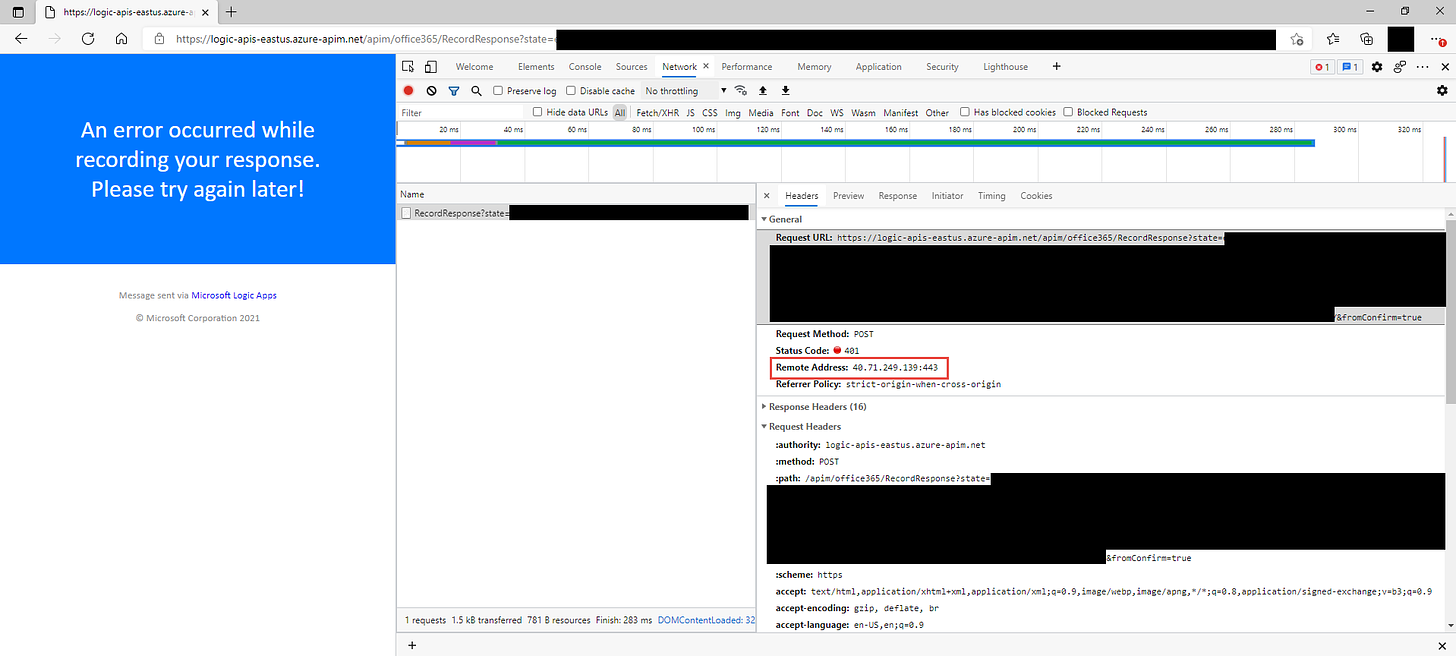
https://logic-apis-eastus.azure-apim.net/apim/office365/RecordResponse?state=XXXX&sig=XXXX&showConfirm=True
To dive deeper I pulled up the developer tools in the browser, I can’t recommend this method enough when troubleshooting portals and websites or just trying to figure out what apis are being called and how when you click save or deploy in the Azure Portal.
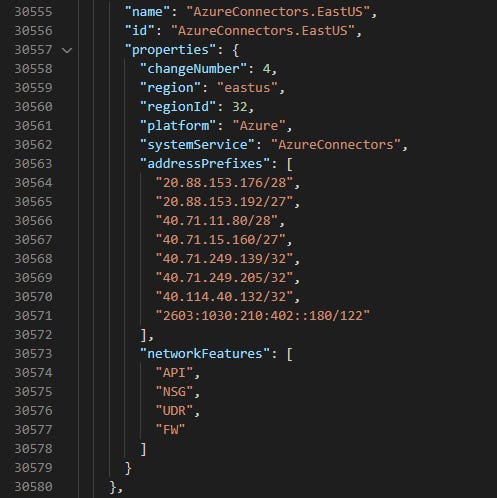
From the remote address I searched within the downloaded document and found a section titled AzureConnectors.EastUS - this makes some sense, since each Unique Connector 1st or 3rd party creates a web api connection Azure resource. After adding these ip address ranges I was able to then click the button and the option successfully post back to the Logic App workflow.
Of course adding ip restrictions this can be automated as Infrastructure as Code with ARM template.
In the meantime do you desire to learn more #AzureSecurityCenter ? Subscribe to the Azure Security Center Wrap