How to create and use Custom RBAC for DataTable Level access
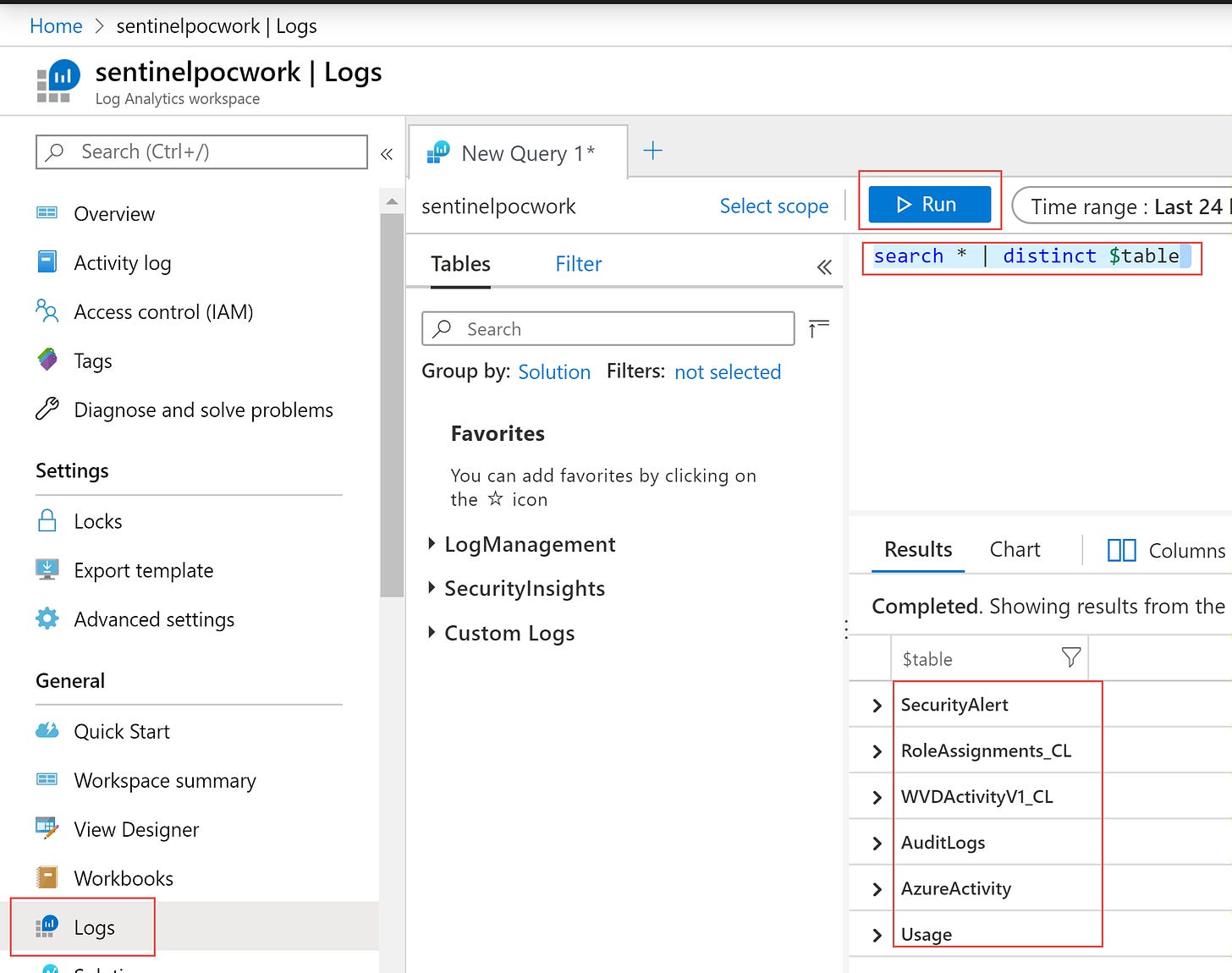
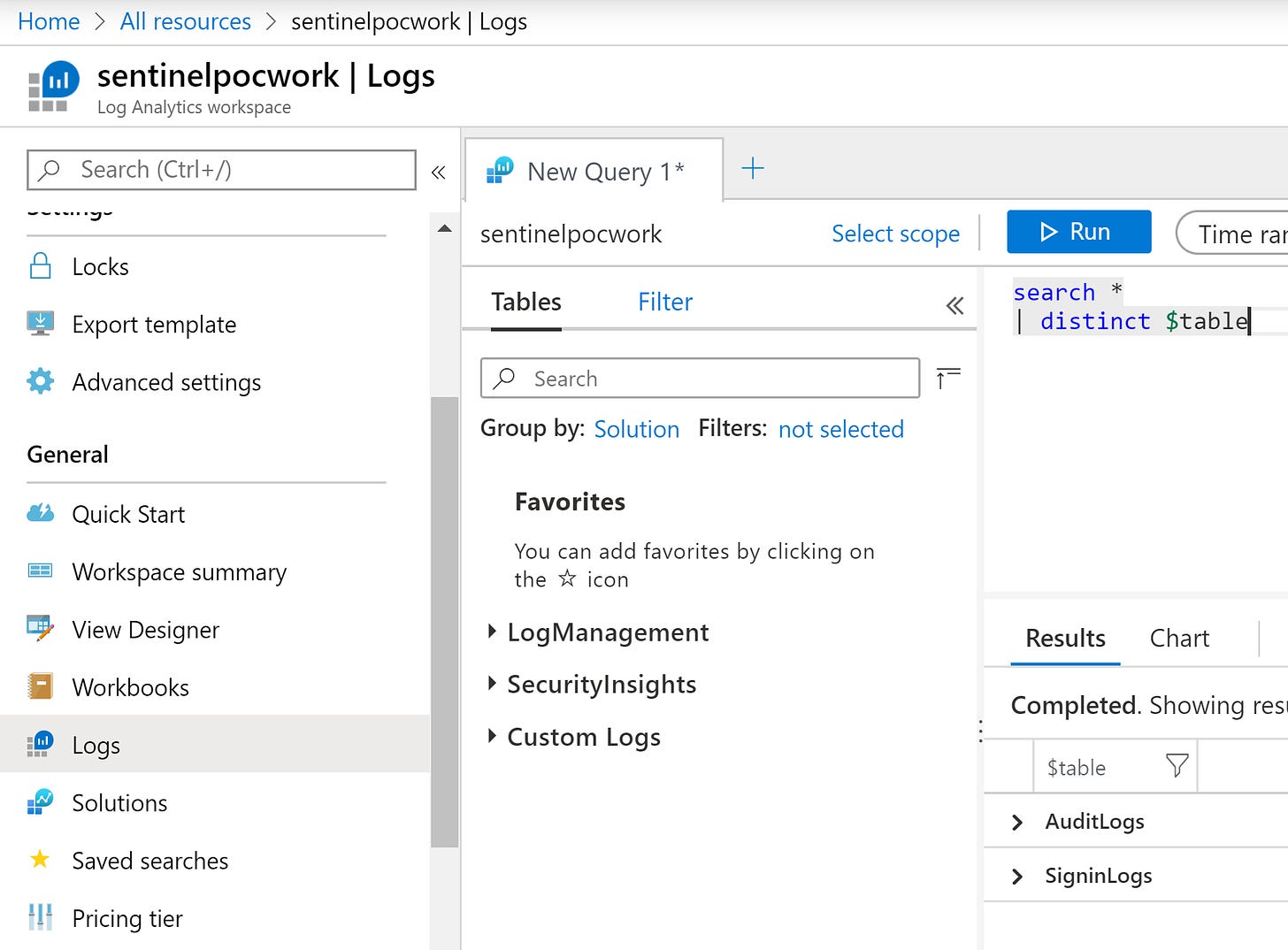
As the Subscription Owner go to the Log Analytics Workspace and Logs blade and search using:
search * | distinct $table
You will then get the different data tables that folks may want to search, use, or access.
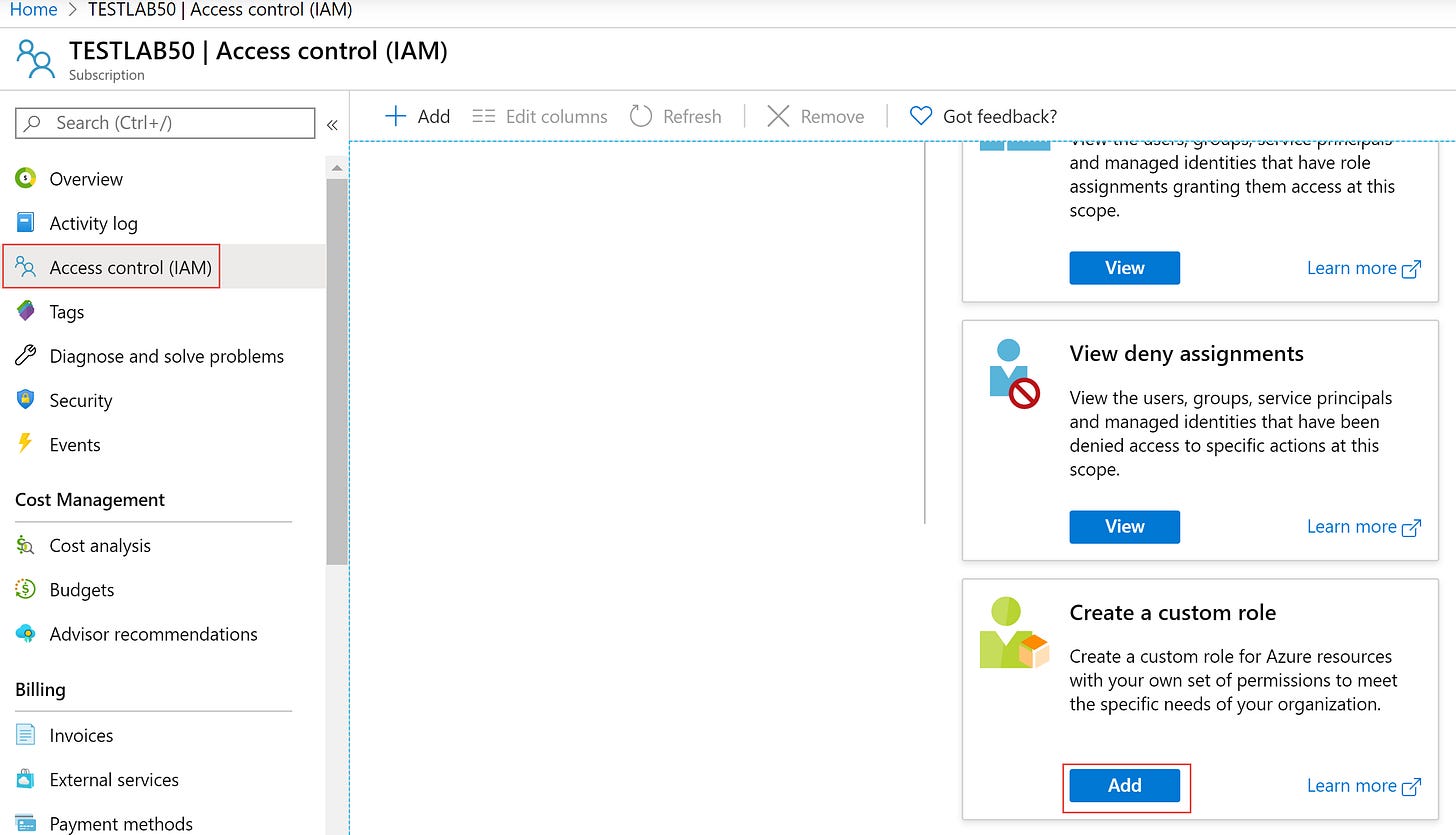
Once you have defined the DataTable needs for a particular user or group you will create a custom RBAC role. To do this you can now do it in the Azure Portal.
Go to the Azure Subscription > Access Control (IAM) > Create a Custom Role
Fill out a logical name for a new Custom RBAC Role, fill in some details.
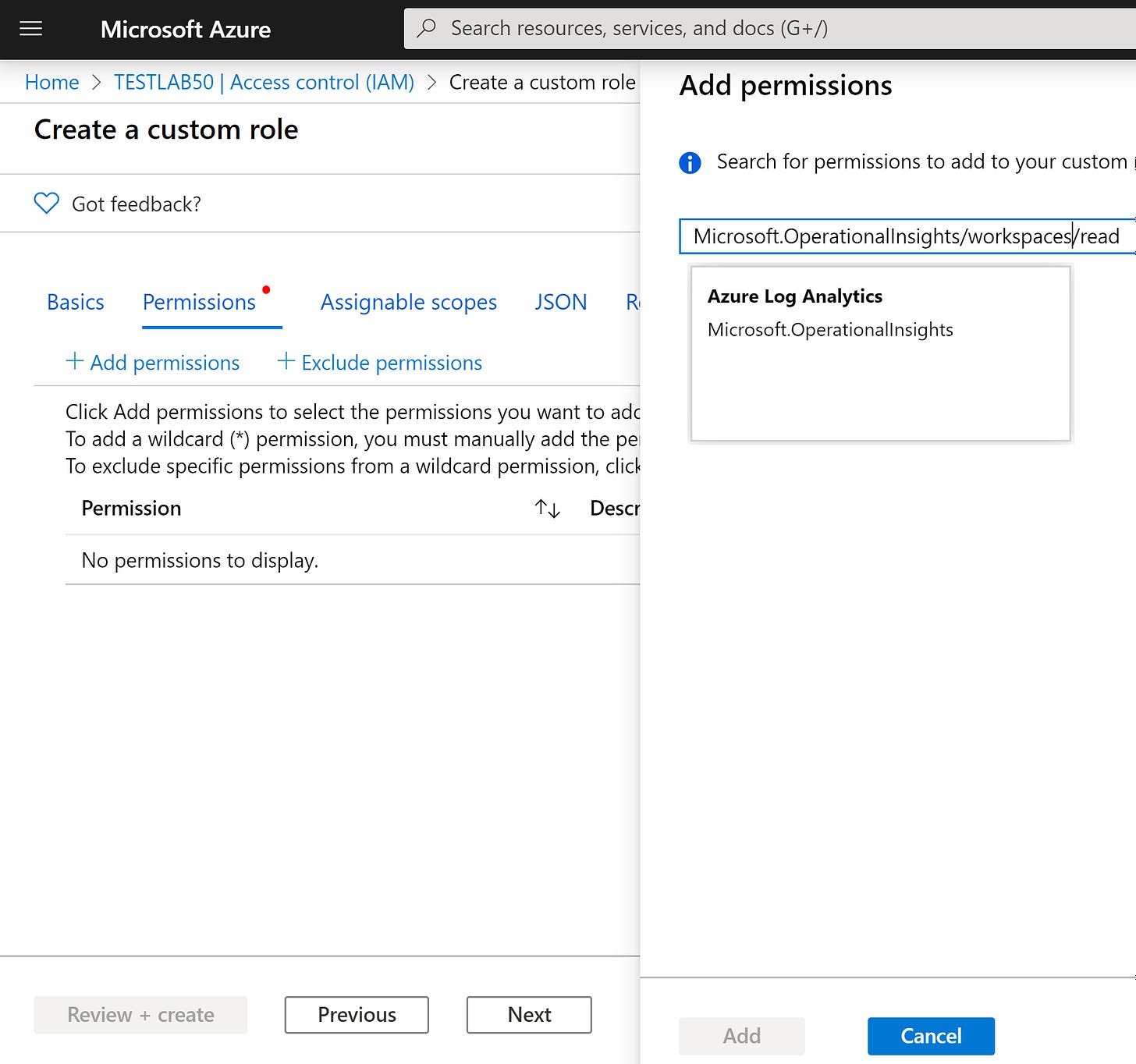
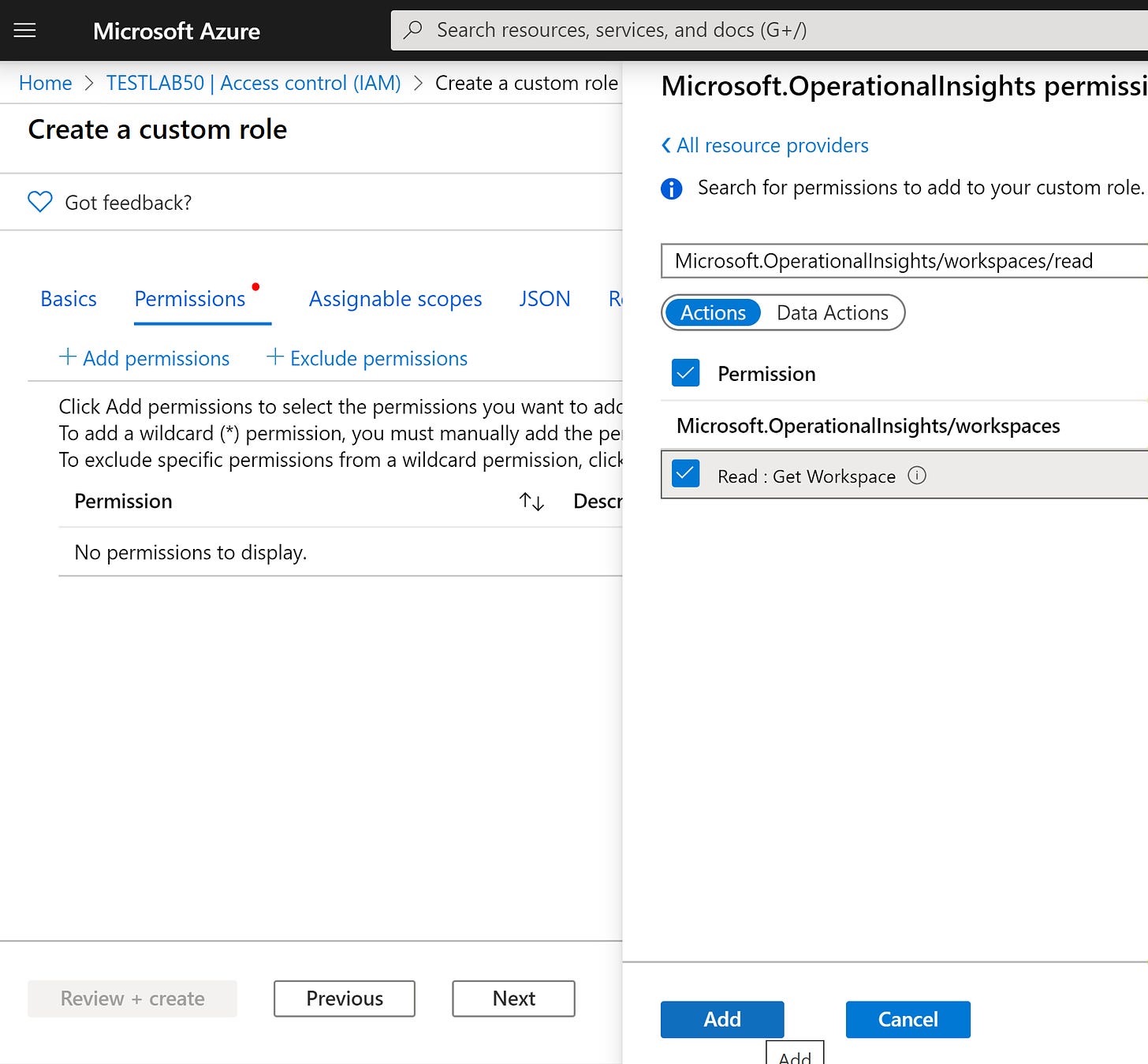
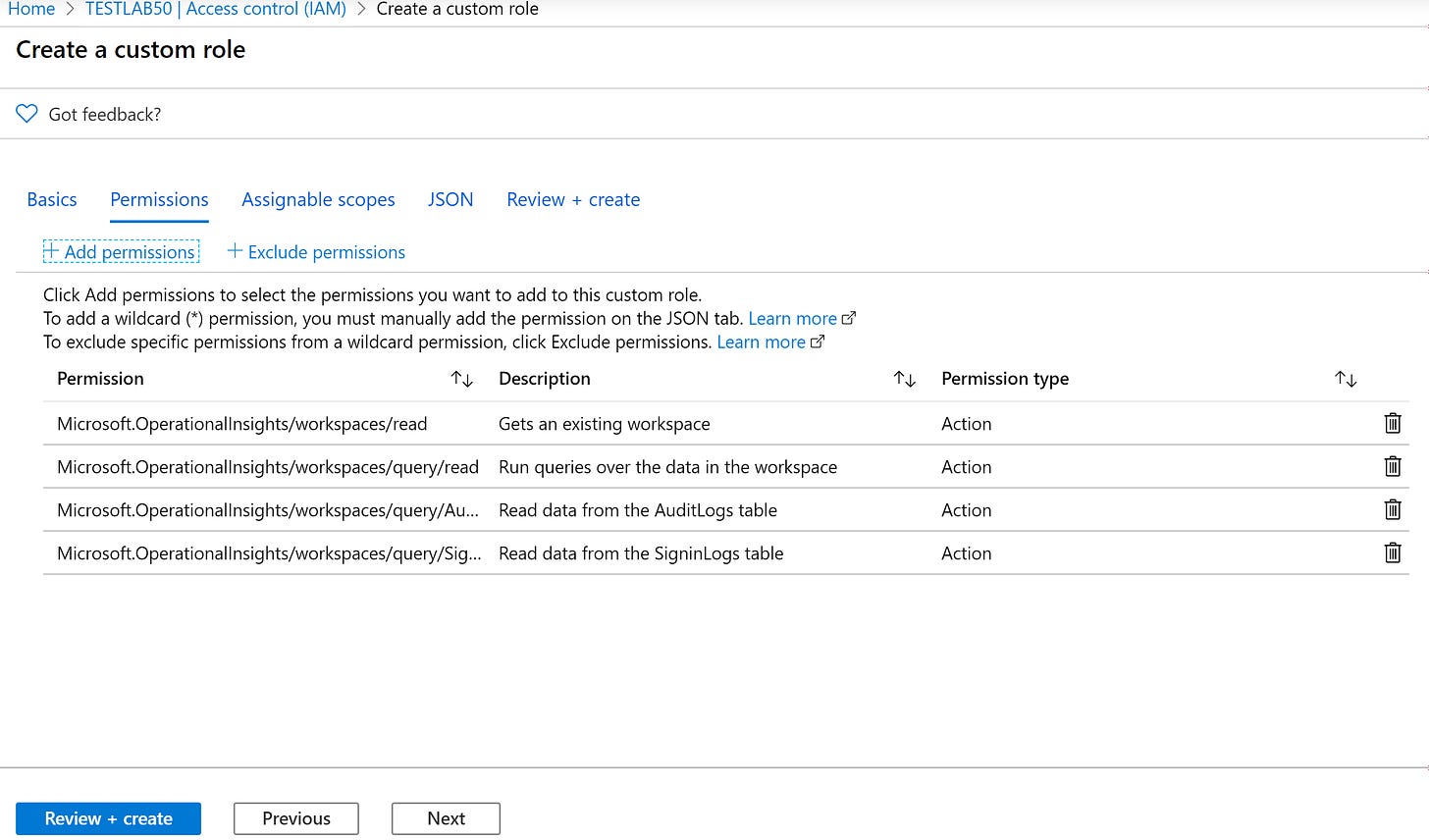
Add permissions and search and add:
Microsoft.OperationalInsights/workspaces/read
Microsoft.OperationalInsights/workspaces/query/read
Microsoft.OperationalInsights/workspaces/query/SigninLogs/read
Microsoft.OperationalInsights/workspaces/query/AuditLogs/read
*Note granting access to Custom logs will grant access to all custom logs, you cannot grant access to ndividual custom logs. Use:
Microsoft.OperationalInsights/workspaces/query/Tables.Custom/read
Replace the highlighted with the data table names you want to grant access.
Source Article: https://docs.microsoft.com/en-us/azure/azure-monitor/platform/manage-access#table-level-rbac
Click next
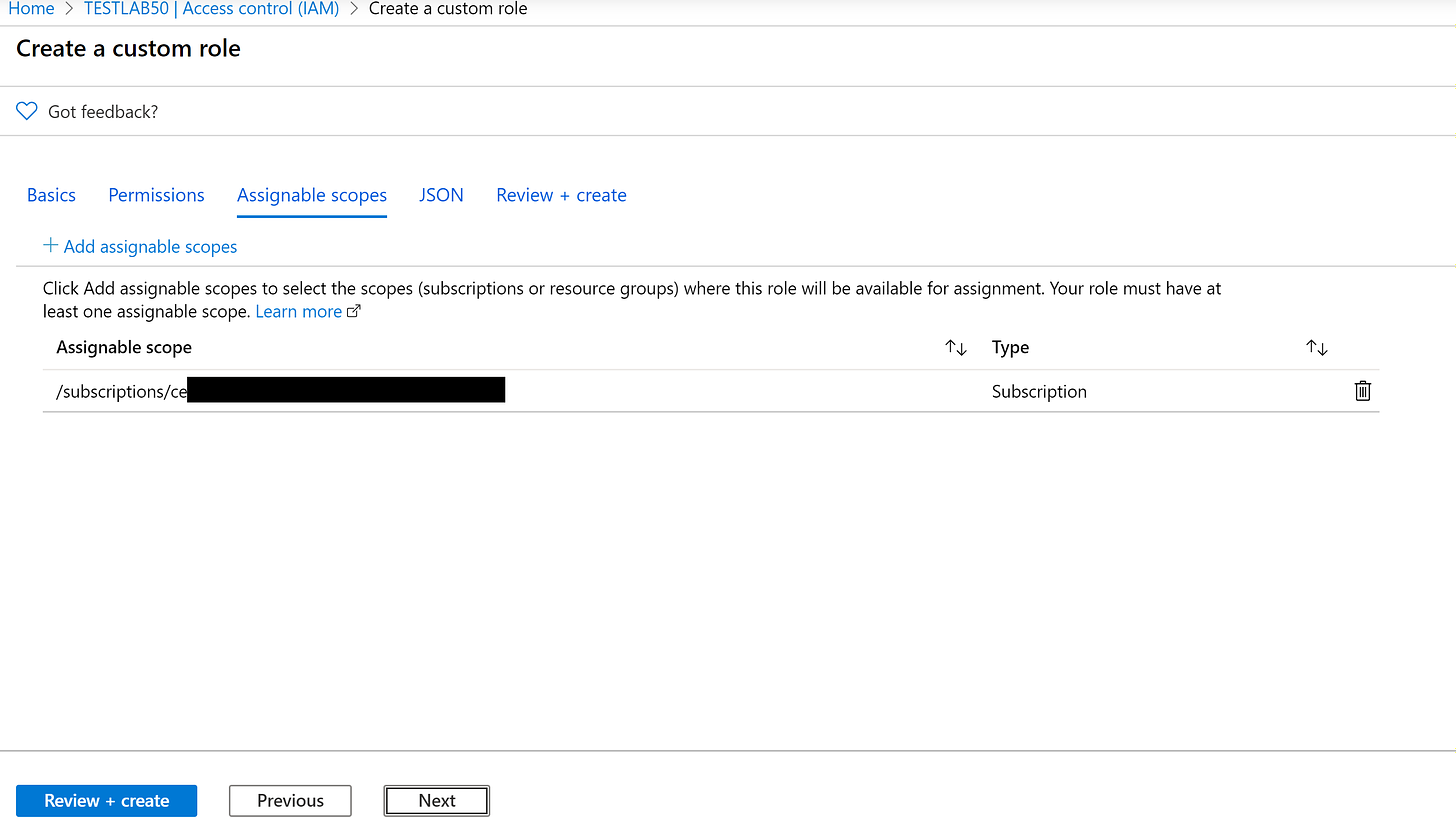
Once completed click Next
Click next
Download the JSON as it can be modified and used to import for any additional new custom Roles you want to create.
Click Review + Create
Create
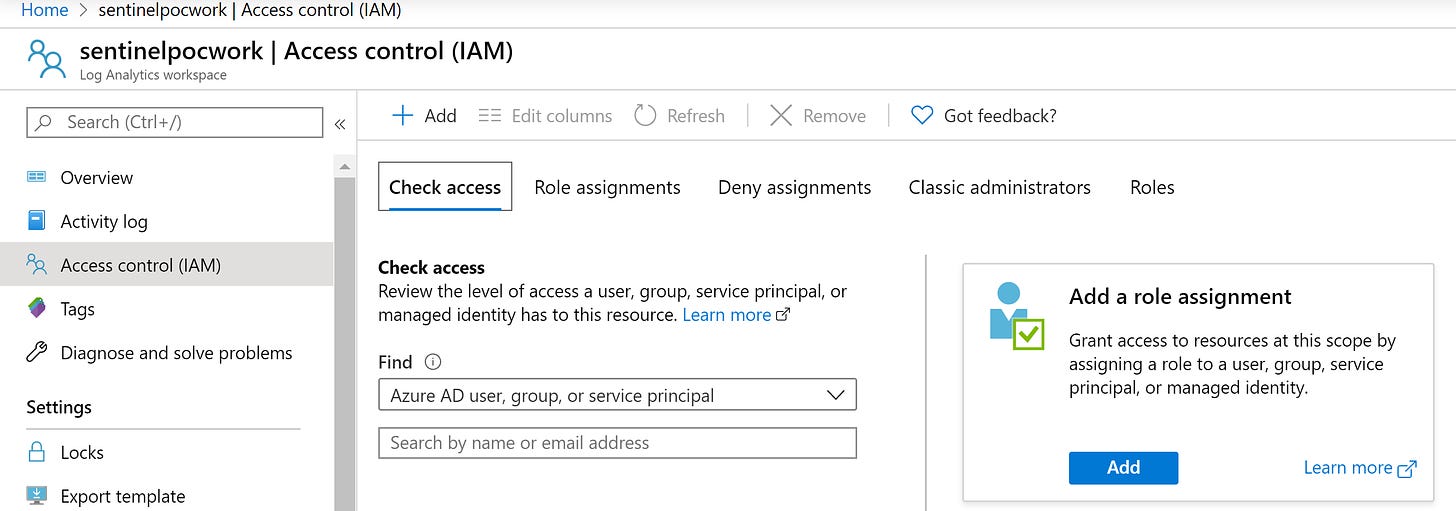
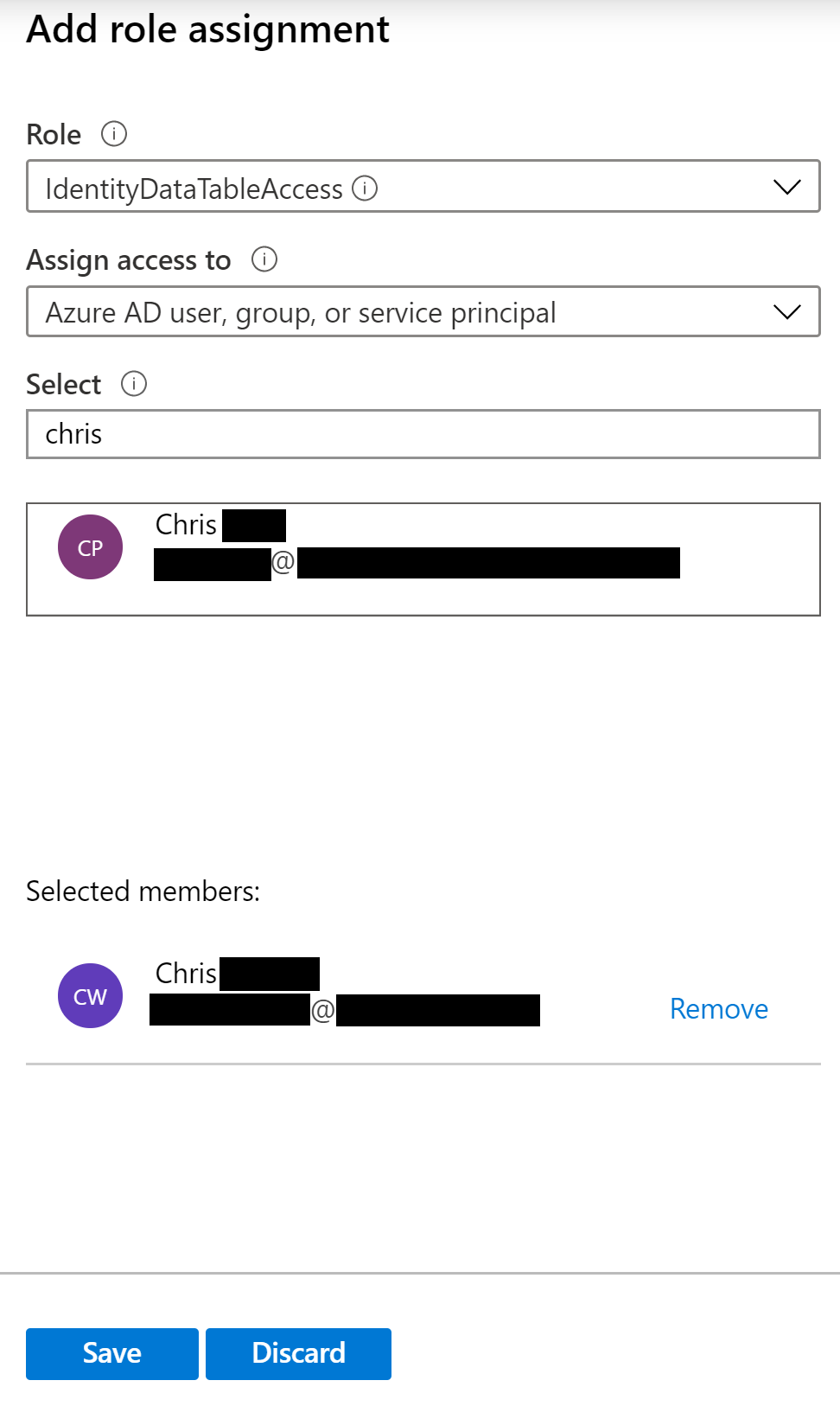
Now we will assign a user or security group access to the new Custom Role we created.
Go to the Log Analytics workspace and Access Control (IAM) blade and Add a role assignment
Choose the new role created and add the user or security group that will access the Logs
Now have the user log into portal.azure.com and access the Log analytics workspace -> logs and run the query again, they will only be able to access and see the DataTables they were granted via the Custom Role
*Note there may be other APIs you may want to grant so the user can perform other activities in the Log Analytics workspace or in Azure portal.