Testing Defender for SQL AMA Solution
AMA edition where are my workload protection test commands ?
Hey all, been awhile since I last posted, so trying to get more committed here in 2024. While working with a customer they wanted to evaluate Defender for SQL. It has been awhile since I looked at Defender for SQL and the deprecation of Microsoft Monitoring Agent (MMA) and solution for Azure Monitor Agent (AMA) is available now. So using the AMA method I allowed Defender for SQL to auto onboard the AMA solution onto a Windows Azure VM and a Arc enabled Windows Server.
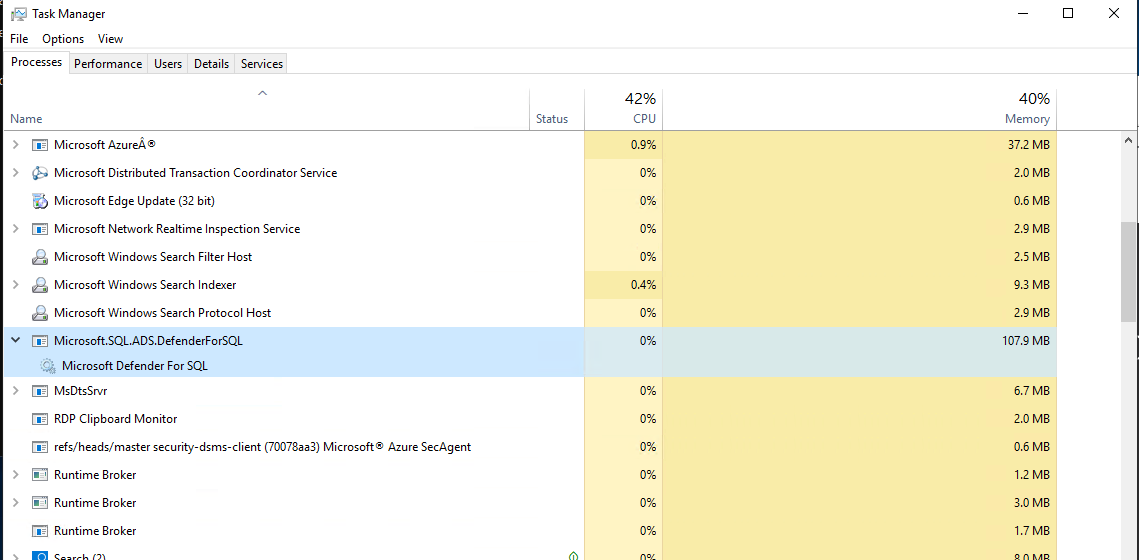
It took awhile I was searching for the old SqlAdvancedThreatProtectionShell.psm1 that came from the Microsoft Monitoring Agent (MMA) solution, but had no success searching through the C:\ drive. Then I remembered my Help Desk roots and opened up Task Manager looking for Defender for SQL running to see if could open up the folder location and I was able to find it was a service and had a location path.
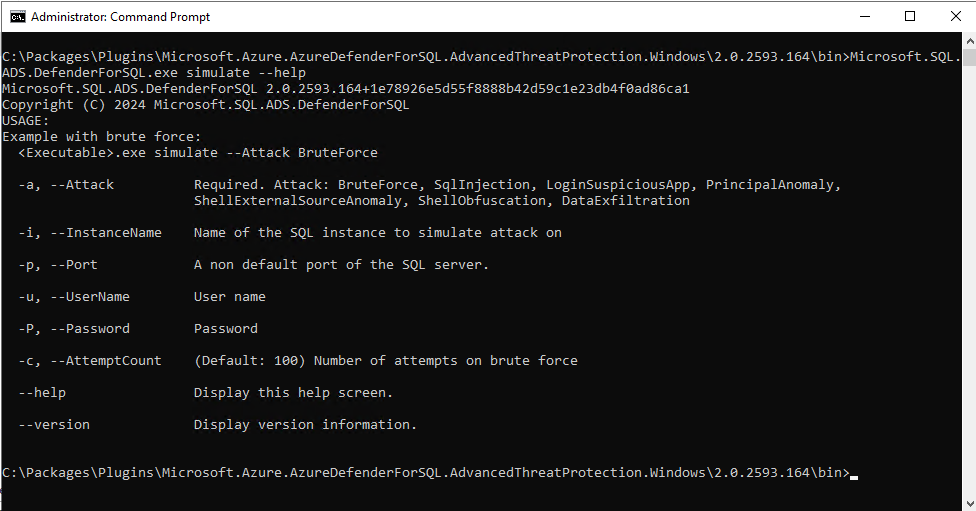
Windows Azure VM or Arc enabled Windows Server: C:\Packages\Plugins\Microsoft.Azure.AzureDefenderForSQL.AdvancedThreatProtection.Windows\2.0.2593.164\bin
Where 2.0.2593.164 is possible to change in the directory path based on version of solution deployed.
Within that directory there is a executable that can be used, with a little —help I started looking around on available commands hoping that there was sone decent help files written.
Microsoft.SQL.ADS.DefenderForSQL.exe —help
Sure enough there were.
Diving a bit deeper we see a simulate, so once more again
Microsoft.SQL.ADS.DefenderForSQL.exe simulate —help
So with some testing you can run a brute force attack like so without having to pass a username and password:
Microsoft.SQL.ADS.DefenderForSQL.exe simulate –Attack BruteForce
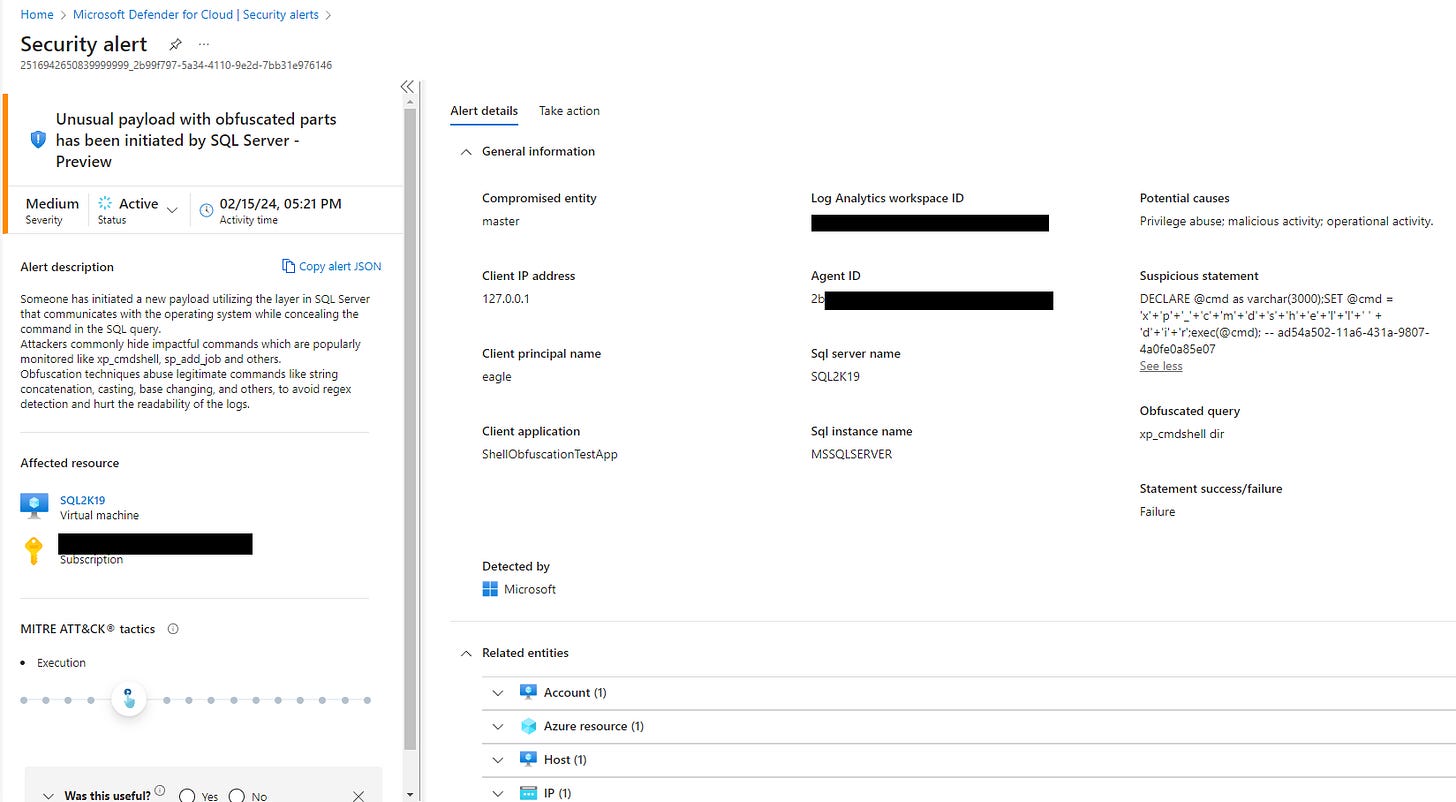
Within a few minutes we receive an alert in Defender for Cloud
As a friendly reminder Microsoft’s NorthStar is “MDC-SIEM-XDR-CoPilot for Security” merging together in the rebranded and redesigning Defender XDR portal.
There also other simulations you can run but the remainder seem to require passing a username and password like so:
Microsoft.SQL.ADS.DefenderForSQL.exe simulate --Attack ShellObfuscation --UserName XXX --Password YYY
The other attacks you could perform where you need to pass a username and password are:
SqlInjection, LoginSuspiciousApp, PrincipalAnomaly, ShellExternalSourceAnomaly, DataExfiltration
Tip: Be sure to take care and use case sensitivity here on the commands and switches.
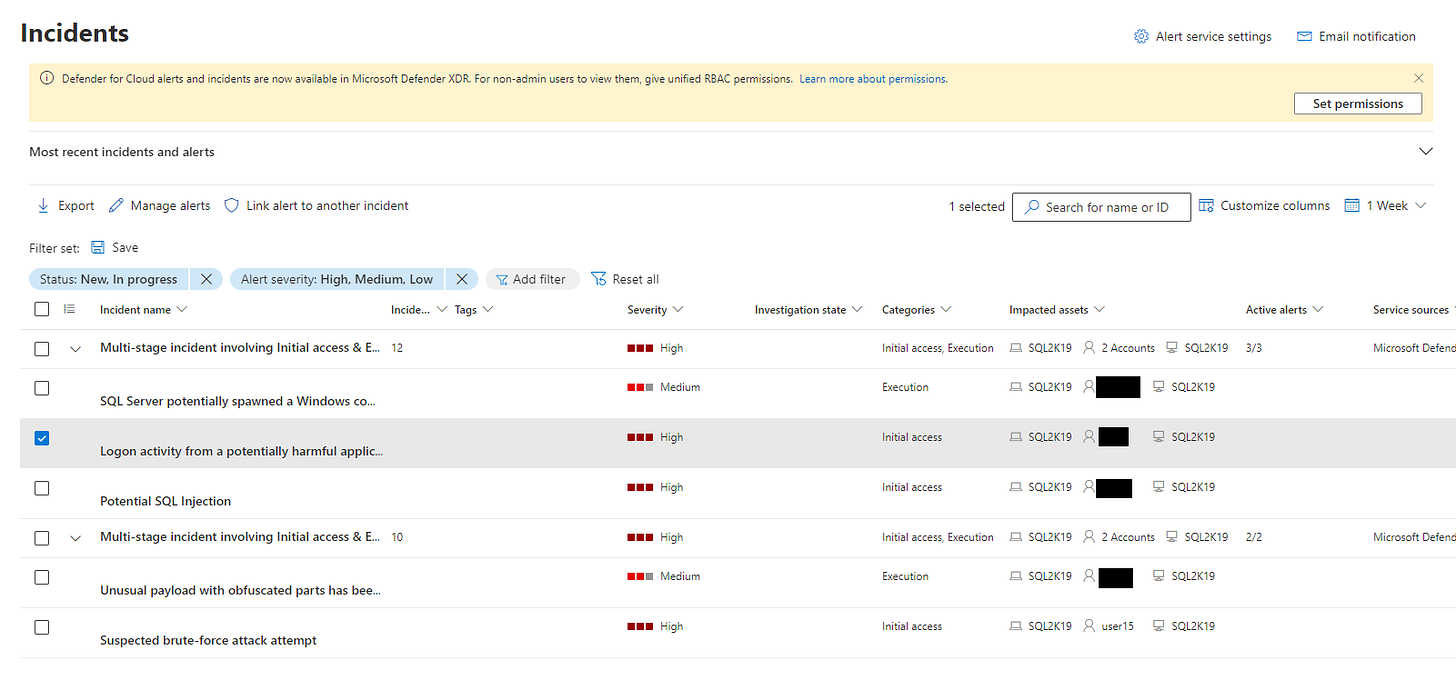
As you test Defender for Cloud and Defender XDR will begin to form the different alerts into an Incident using Fusion.
And that is how you can test Defender for SQL threat protection easily as you are evaluating. This capability is a great way to understand the Defender for SQL alert schema as it pertains to each alert as well as you run through each simulation and look at the alert structure, descriptions, evidence and commands or other artifacts used in the simulated attack. It’s possible in a future post I’ll dig deeper using ProcMon or a debugger to get more insights into the simulated attack.
But for now stay Synthwave.